Cyber Security
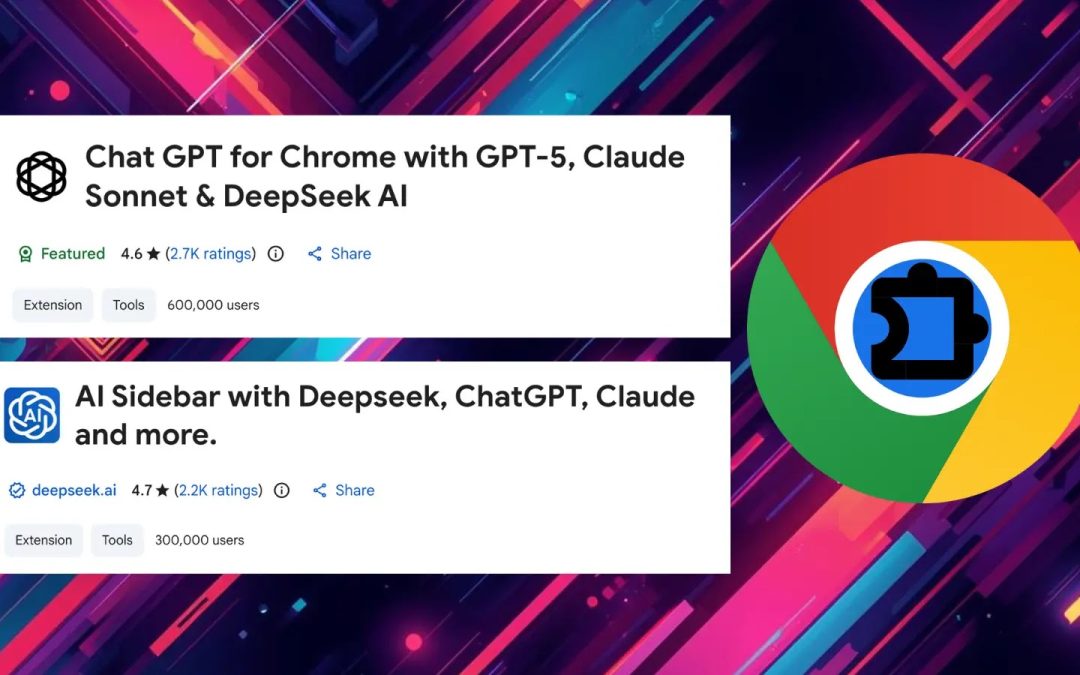
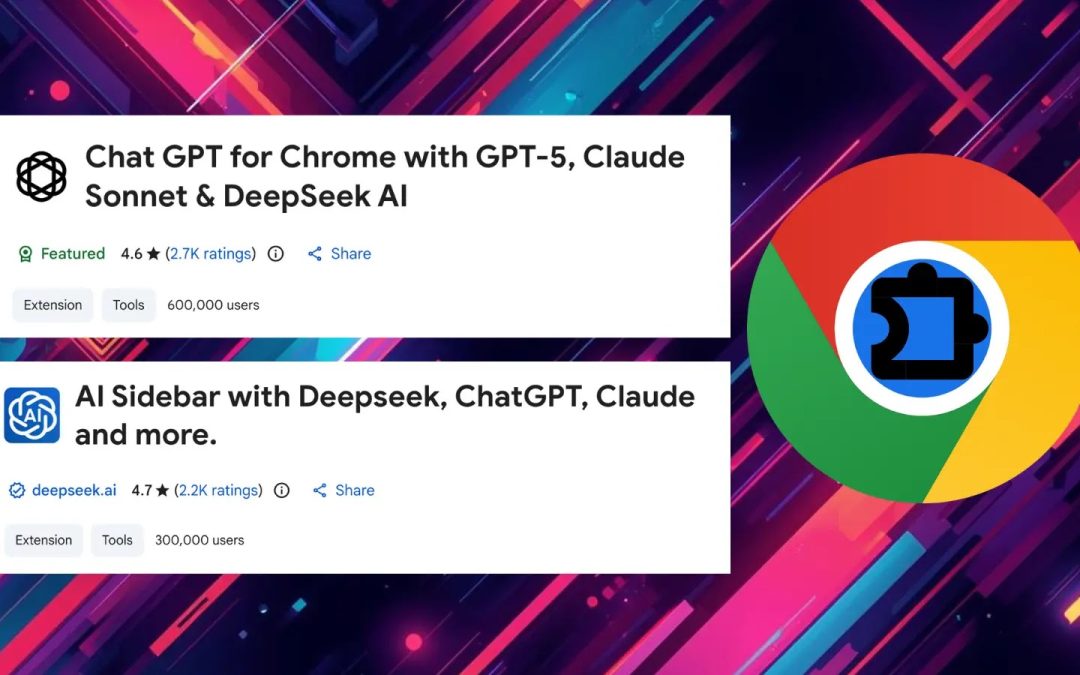
“`html Two malicious Chrome extensions have jeopardized more than 900,000 users by covertly extracting ChatGPT and DeepSeek conversations, along with comprehensive browsing histories, to the attackers’ servers. Uncovered by OX Security analysts, the...

Cyber Security
“`html WhatsApp’s multi-device encryption framework has persistently exposed metadata, permitting adversaries to identify users’ device operating systems, facilitating targeted malware transmission. Recent studies underscore partial corrections by Meta, yet...

Cyber Security
“`html Resecurity implements artificial data honeypots to outwit threat actors, converting reconnaissance into useful intelligence. A recent operation not only ensnared an Egyptian-associated hacker but also misled the ShinyHunters collective into believing...
Cyber Security
“`html An alarming cycle of cybercrime has arisen where pilfered credentials from infostealer malware permit cybercriminals to commandeer authentic business sites and convert them into platforms for distributing malware. Recent findings from the Hudson Rock...

Cyber Security
“`html More than 10,000 Fortinet firewalls globally remain exposed to CVE-2020-12812, a vulnerability allowing bypass of multi-factor authentication (MFA) identified over five and a half years ago. Recently, Shadowserver incorporated the issue into its daily...