Cyber Security
“`html The Indian authorities are presently reviewing a controversial suggestion from the telecommunications sector that would require smartphone manufacturers to activate “always-on” satellite location tracking. This initiative has ignited considerable dissent...
Cyber Security
“`html A comprehensive offensive security toolkit, NETREAPER, created by OFFTRACKMEDIA Studios, amalgamates more than 70 penetration testing tools into a single, intuitive command-line interface. This advancement eradicates the disorder of managing multiple...

Cyber Security
“`html A perilous new Android banking malware titled FvncBot was first detected on November 25, 2025. This malicious software is crafted to expropriate sensitive financial data by recording keystrokes, capturing screens, and injecting counterfeit login...

Cyber Security
“`html Experts in security from the SAFA group have revealed four kernel heap overflow weaknesses in Avast Antivirus, all linked to the aswSnx kernel driver. The vulnerabilities, currently cataloged as CVE-2025-13032, might enable a local attacker to elevate...
Cyber Security
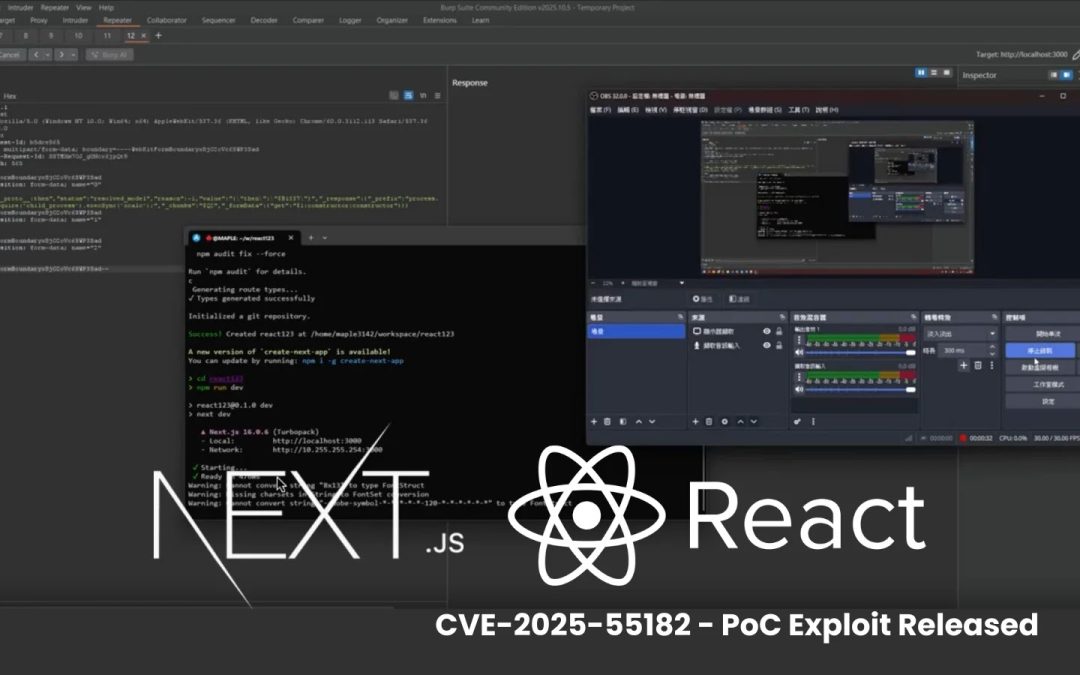
“`html A proof-of-concept (PoC) exploit pertaining to CVE-2025-55182, a critical remote code execution (RCE) vulnerability in React Server Components, emerged publicly this week, raising concerns for developers globally. Referred to as “React2Shell” by several...