Cyber Security
A rootkit is a form of malicious software created mainly to grant unauthorized access and control over a computer system while concealing its presence. Detecting and eliminating them can pose a challenge as they function at a deep level within the operating system. By...
Cyber Security
Given the increasing complexity and widespread nature of internet dangers, the demand for efficient hazard management has never been more critical. Defining a strategy to mitigate hazards is a challenge on its own, but putting a value on risks in a manner that...
Cyber Security
The CISA has issued an urgent warning about the active exploitation of vital weaknesses in Synacor’s Zimbra Collaboration and Ivanti’s Endpoint Manager (EPM). Firms utilizing these products are encouraged to promptly address possible dangers. CVE-2024-45519: Synacor...
Cyber Security
The upsurge in utilization of artificial intelligence (AI) in the last couple of years has significantly transformed not just software but also hardware. As AI adoption continues to progress, computer manufacturers have discovered in AI a chance to enhance end-user...
Cyber Security
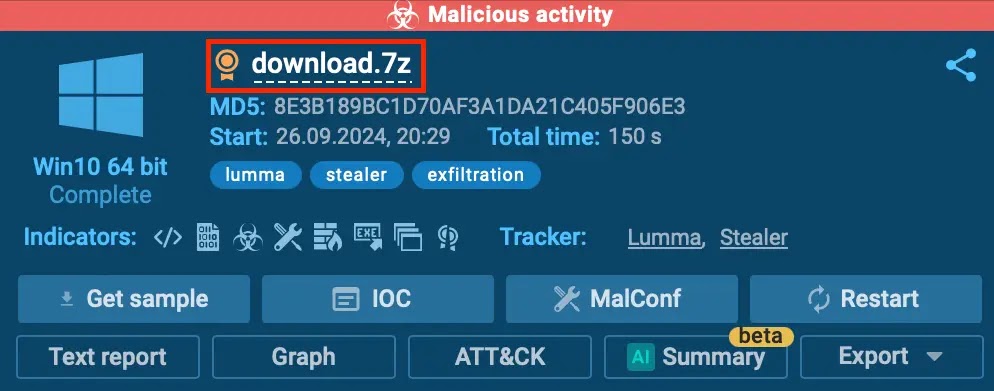
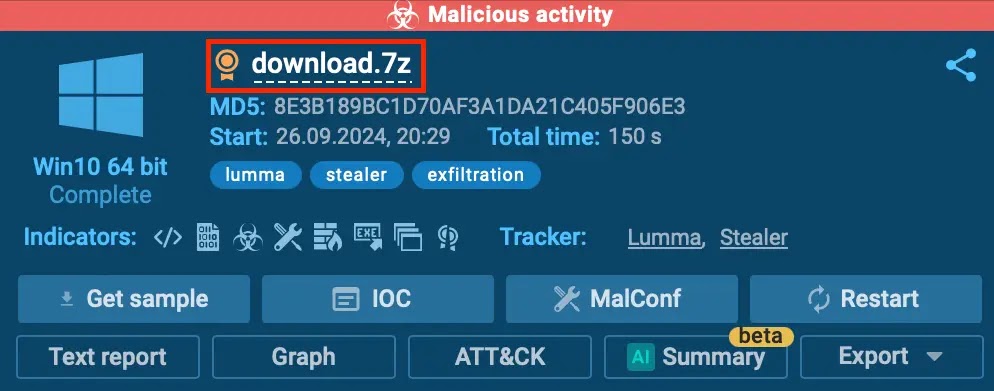
Signs of Intrusion (SOIs) are vital clues that cybersecurity experts utilize to “spot,” “probe,” and “alleviate” security risks. As these electronic hints harbor “questionable IP addresses,” “malware...