Cyber Security
“`html Notepad++ has officially unveiled version 8.9.3, providing essential security fixes, performance improvements, and solutions for ongoing crash challenges. This upgrade completes the text editor’s shift to a highly efficient XML parser, rectifying several...
Cyber Security
“`html Spam Filter Tools Spam filtering solutions utilize sophisticated algorithms and machine learning methodologies to recognize and eliminate unwanted email communications. They examine email content, the sender’s trustworthiness, and behaviors to...

Cyber Security
“`html Cybersecurity shares fell drastically on Friday after disclosures that Anthropic has commenced trials of “Mythos,” an extremely potent new AI model equipped with sophisticated vulnerability-detection abilities. Anthropic is currently testing a new...

Cyber Security
“`html The European Commission has formally acknowledged a cyber intrusion following a deliberate cyber breach that compromised its Amazon Web Services (AWS) account. Identified on March 24, the breach specifically impacted the external cloud ecosystem that...
Cyber Security
“`html Anthropic has unintentionally uncovered extremely confidential internal documents, disclosing the emergence of a formidable, unreleased AI model referred to as “Claude Mythos.” The breach, which originates from an unprotected and publicly indexed data...
Cyber Security
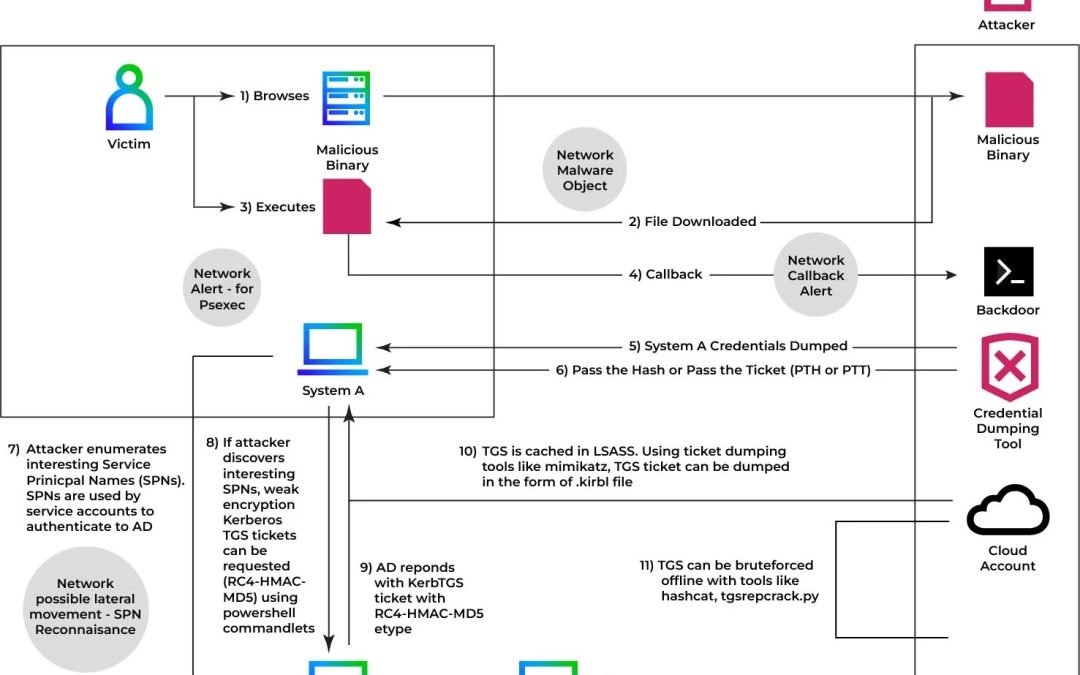
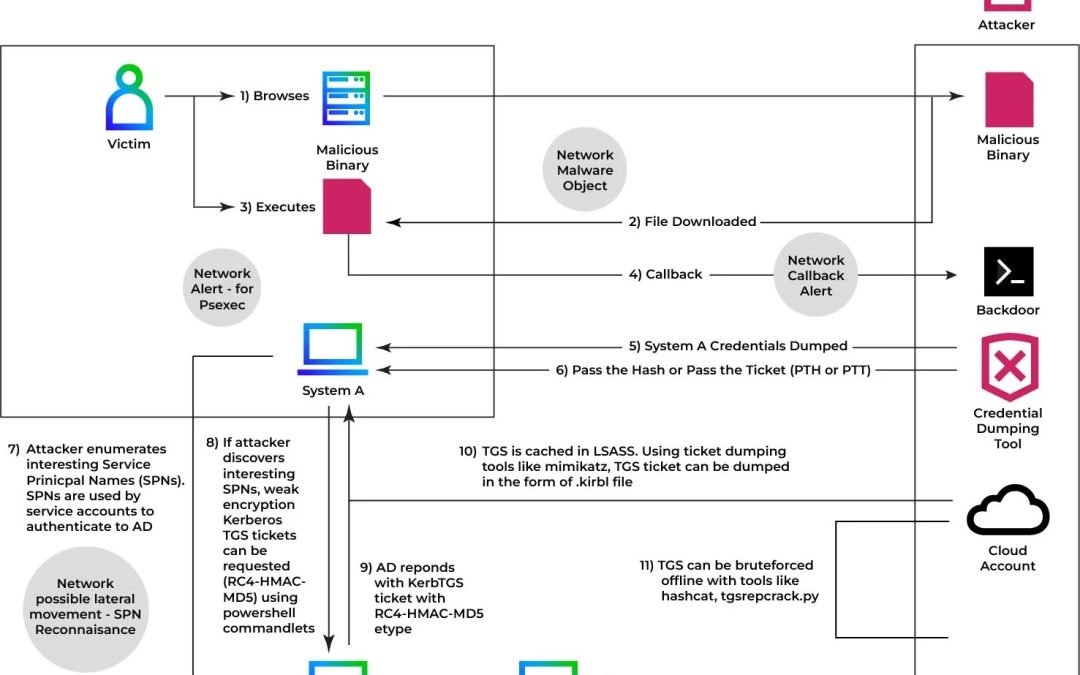
“`html An advanced iteration of Kerberoasting referred to as the “Ghost SPN” assault enables attackers to gather Active Directory credentials while eliminating all evidence of their operations, making conventional detection frameworks largely oblivious to the...