Cyber Security
“`html UAC‑0099, a sophisticated threat actor collective that has been operational since at least 2022, continues to represent a serious cybersecurity hazard through its evolving cyber-espionage initiatives aimed at Ukrainian governmental entities, military...
Cyber Security
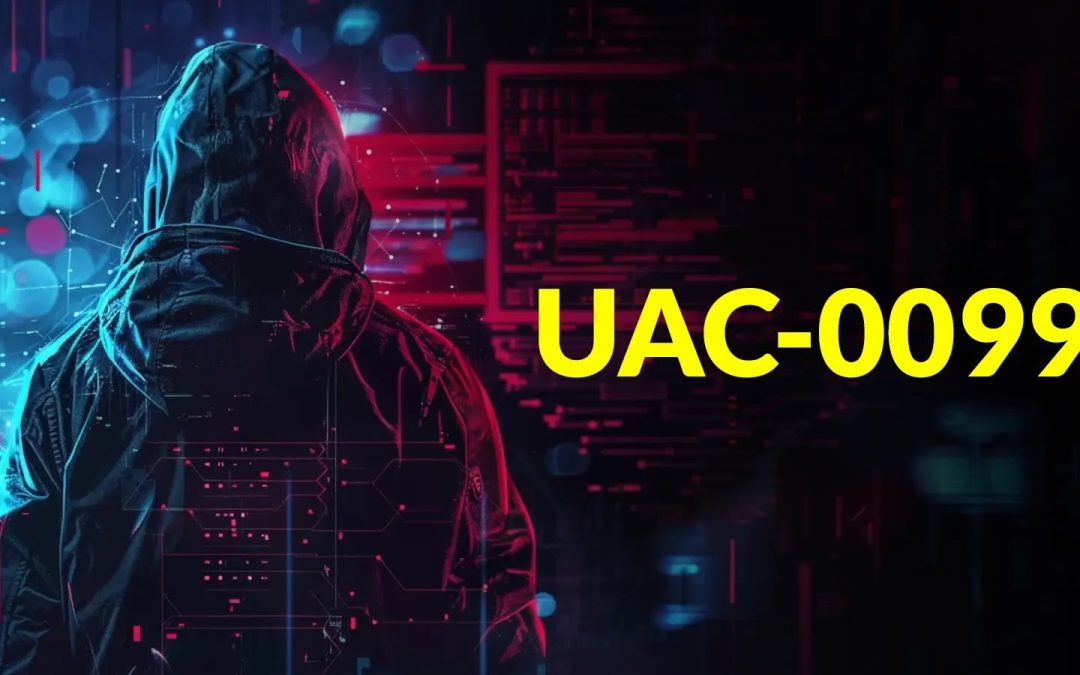
“`html LAS VEGAS — At DEF CON 33 cybersecurity conference, researchers Yair and Shahak Morag from SafeBreach Labs revealed a novel category of denial-of-service (DoS) attacks, termed the “Win-DoS Epidemic.” The pair shared their discoveries, which encompass four...

Cyber Security
“`html Darknet bazaars, functioning outside the grasp of conventional payment processors and legal frameworks, depend on escrow mechanisms to safeguard cryptocurrency exchanges between purchasers and sellers. These mechanisms, incorporating multisignature...
Cyber Security
“`html A complex new malware framework known as CastleBot has surfaced as a considerable danger to cybersecurity, functioning as a Malware-as-a-Service (MaaS) platform that permits cybercriminals to launch various harmful payloads, including infostealers and...

Cyber Security
“`html Cyber offenders have started taking advantage of Scalable Vector Graphics (SVG) files as advanced attack channels, converting what appear to be innocuous image files into powerful phishing tools capable of running harmful JavaScript on Windows platforms....
Cyber Security
Two advanced ransomware operations have surfaced as major threats to managed service providers (MSPs) and small enterprises, with the Akira and Lynx groups employing sophisticated attack methods that merge stolen credentials with vulnerability exploitation. These...