Cyber Security
“`html Secure code review is an essential security practice that thoroughly scrutinizes software source code to uncover and rectify security vulnerabilities prior to their deployment in production environments. This detailed assessment acts as a proactive...
Cyber Security
“`html Ransomware perpetrators have increasingly resorted to a refined new malware instrument known as Skitnet, also referred to as “Bossnet,” to improve their post-exploitation capabilities and bypass conventional security protocols. First surfacing on...
Cyber Security
A sophisticated new data-exfiltrating malware crafted in the Rust programming language has surfaced, showcasing advanced abilities to retrieve sensitive information from both Chromium-based and Gecko-based web browsers. The malware, referred to as Myth Stealer,...
Cyber Security
Kali GPT, a tailored AI model based on the GPT-4 framework, has been specifically designed to integrate fluidly with Kali Linux, providing unparalleled assistance for offensive security experts and learners alike. Kali GPT signifies a major advancement in the...

Cyber Security
A complex malware distribution initiative has exploited over 140 GitHub repositories to target novice cybercriminals and users of gaming cheats, marking one of the most extensive documented instances of supply chain attacks on the platform. The repositories, disguised...
Cyber Security
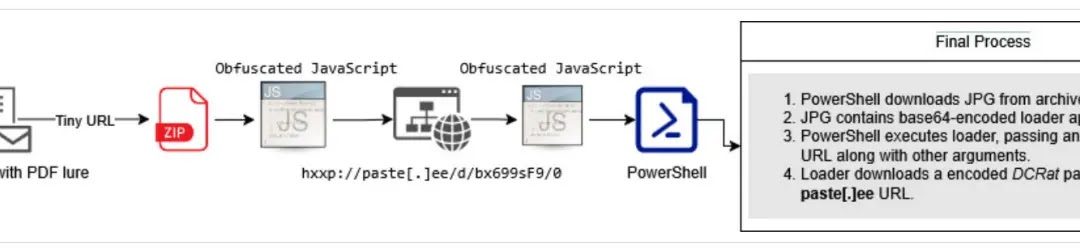
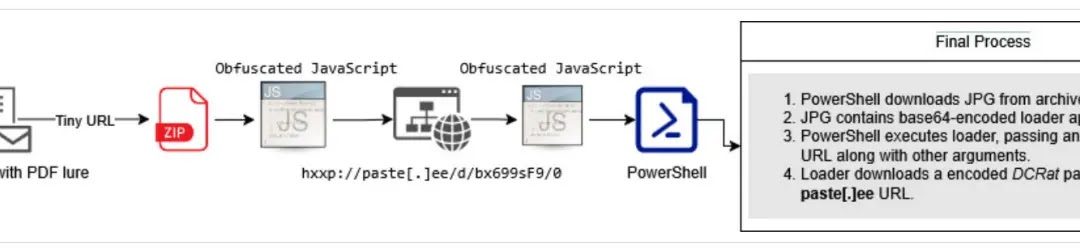
An elaborate malware initiative aimed at Latin American users has surfaced as a notable peril to the region’s financial industry, with cybercriminals utilizing the DCRat banking trojan through intricate phishing strategies intended to expropriate financial...