“`html
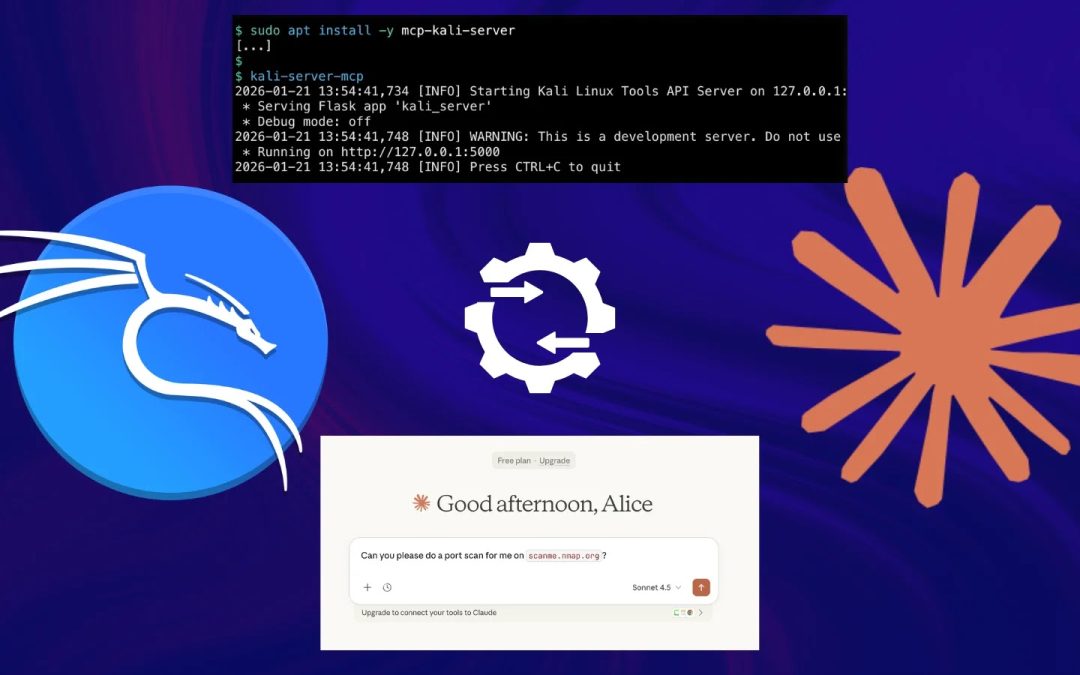
Kali Linux has officially launched a built-in AI-supported penetration testing workflow, allowing security experts to issue commands in natural language via Anthropic’s Claude AI, which are subsequently converted into live terminal commands within a Kali Linux environment, all facilitated by the open-source Model Context Protocol (MCP).
This novel workflow, detailed by the Kali Linux development team in early 2026, transcends conventional terminal-based command execution.
Rather than manually utilizing instruments like Nmap or Gobuster, a penetration tester can simply input a request such as “Port scan scanme.nmap.org and verify if a security.txt file is present,” and Claude AI will autonomously interpret, plan, execute, and provide results.
This functionality is enabled through a tri-component architecture:
- UI Layer: Claude Desktop operating on macOS (or Windows), acting as the natural language gateway to the LLM.
- Execution Layer: A Kali Linux machine (local or cloud-based) running mcp-kali-server, a minimal API bridge that connects security tools to MCP clients.
- Intelligence Layer: Anthropic’s Claude Sonnet 4.5 model, hosted in the cloud, which handles prompts and orchestrates tool invocations.
How the MCP Bridge Operates
The Model Context Protocol (MCP), initially launched by Anthropic to the public in 2024, offers a standardized method for integrating functions, data, and controls from external systems into AI workflows.
Instead of creating custom API integrations for each tool, MCP functions as a universal connector, enabling the LLM to maintain contextual awareness across several tool interactions within a single session.
In the Kali integration, when a user issues a prompt, Claude identifies the necessary security tool and sends a structured request to the mcp-kali-server.

The server performs the command on the Kali host, sends back structured output to the LLM, which then interprets the results, conveys findings to the user, and if necessary, automatically iterates with follow-up commands to complete the original request.
This establishes a self-sustaining loop: prompt → plan → execute → interpret → re-execute if needed.
Claude AI and Kali Linux
The setup necessitates SSH-based communication between the macOS client and the Kali server, utilizing key-based authentication (ed25519) for passwordless access. On the Kali side, mcp-kali-server is installed using apt and operates a Flask-based API on localhost:5000, serving as the command execution bridge.

The MCP client configuration in Claude Desktop is adjusted via claude_desktop_config.json to connect to the Kali instance over SSH, using stdio transport. Key penetration testing tools supported by the MCP server comprise:
- Nmap — network and port scanning
- Gobuster / Dirb — directory and web path enumeration
- Nikto — web server vulnerability analysis
- Hydra / John the Ripper — credential brute-forcing
- Metasploit Framework — exploitation and post-exploitation
- SQLMap / WPScan — database injection and WordPress auditing
- Enum4linux-ng — SMB/Windows enumeration
During evaluations recorded by the Kali team, a prompt requesting a port scan of scanme.nmap.org prompted Claude to check tool availability, execute nmap -sV scanme.nmap.org, identify open ports on 80/TCP and 443/TCP, and report findings, all without any manual command input.

The server logs verified real-time execution: checks on tool availability, the invocation of Nmap, and structured HTTP responses from the Flask API.
Security analysts warn that MCP-enabled AI workflows present new attack vectors, encompassing prompt injection, over-permissioned tool access, and inadequate audit logging.
Red Hat and Fluid Attacks both advise implementing least-privilege access, validating all inputs, requiring human-in-the-loop approval for high-risk commands, and maintaining immutable execution logs for any production or approved engagement.
The Kali team itself underscores that this is a method, not necessarily the optimal method, and users concerned about data privacy should thoroughly assess whether directing commands through a cloud-hosted LLM aligns with their engagement scope and client agreements.
This integration signifies a significant transformation in how AI is being utilized within offensive security tools. By combining Claude’s reasoning abilities with MCP’s tool-execution layer, even less experienced testers receive marked, explainable guidance throughout intricate workflows from initial reconnaissance to vulnerability appraisal, all within a conversational interface.
As MCP adoption accelerates throughout the security sector, AI-enhanced penetration testing is rapidly evolving from experimental to mainstream.
“`