Cyber Security
AI-powered coding tools are rapidly changing how developers build and ship software. But as these tools enter everyday development pipelines, they are also opening new doors for attackers. A recently uncovered vulnerability in a widely used AI coding assistant shows...

Cyber Security
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical Linux kernel vulnerability, tracked as CVE-2022-0492, to its Known Exploited Vulnerabilities (KEV) catalog, warning that the flaw is being actively leveraged in real-world attacks....

Cyber Security
Last year, a botnet hurled 31.4 Tbps of junk traffic at a single target—enough data to stream every Netflix movie at once. The record-shattering flood forced boards, regulators, and cloud teams to ask one question: are we sure our defenses work when the internet turns...
Cyber Security
Cisco has disclosed a high-severity vulnerability in its Catalyst SD-WAN Manager that is actively being exploited in the wild, allowing attackers to execute arbitrary commands with root privileges. The issue, tracked as CVE-2026-20245, carries a CVSS score of 7.8 and...
Cyber Security
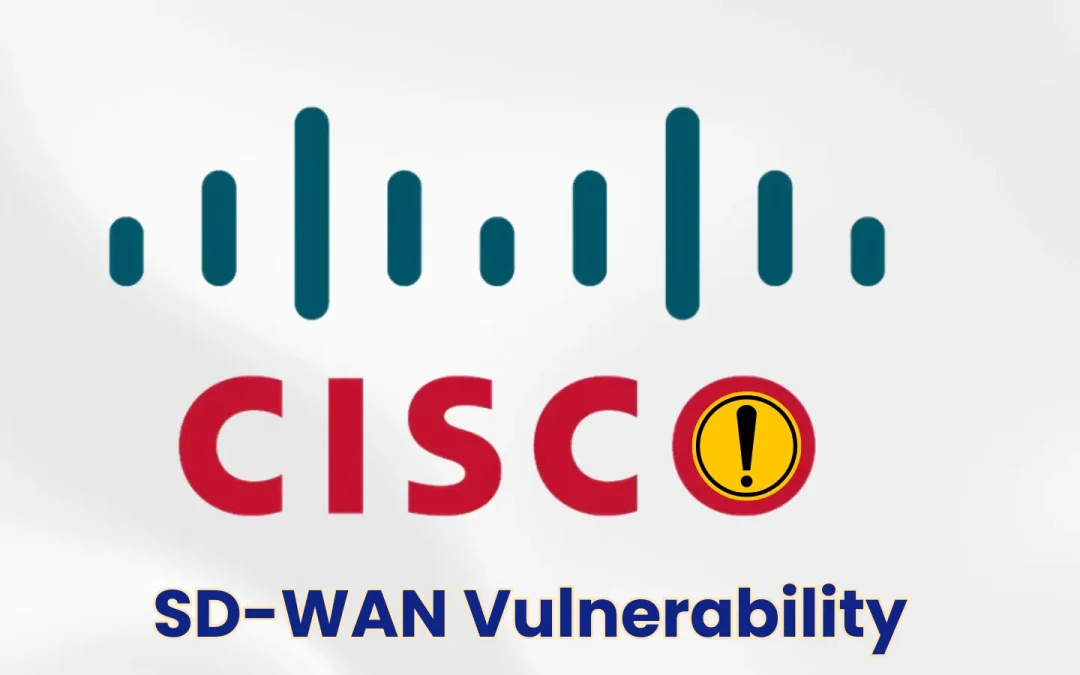
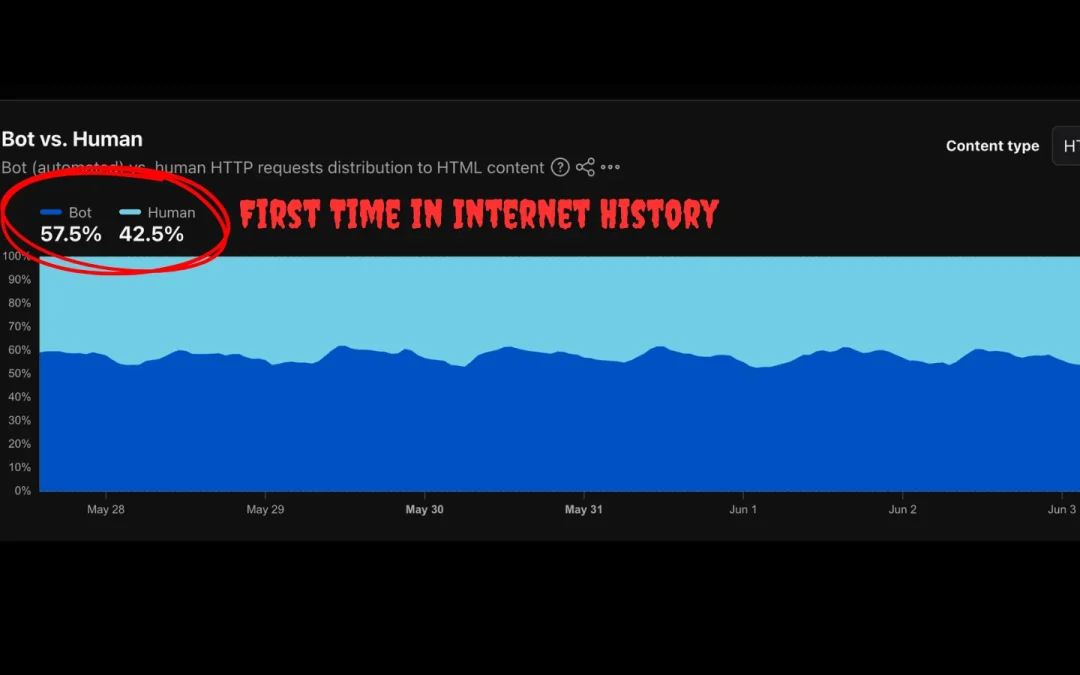
For the first time ever, automated bots have officially overtaken human users in global internet traffic, and the shift is accelerating faster than even industry leaders predicted. Bots Surpass Humans in Web Traffic According to data from Cloudflare Radar, bots now...

Cyber Security
A critical security vulnerability in Visual Studio Code’s webview implementation allows attackers to steal GitHub OAuth tokens, including read/write access to private repositories, simply by tricking a victim into clicking a single malicious link. The bug was publicly...

Cyber Security
A critical security vulnerability in the popular WP Maps Pro WordPress plugin could allow attackers to gain full control of affected websites by creating unauthorized administrator accounts. The flaw, tracked as CVE-2026-8732 with a CVSS score of 9.8, impacts all...

Cyber Security
Microsoft has clarified its stance, reducing perceived legal threats and reaffirming its commitment to coordinated vulnerability disclosure, following significant backlash from the security research community. In a carefully worded statement released in late May 2026,...

Cyber Security
Microsoft has rolled out a new cumulative update, KB5089573, for Windows 11 versions 25H2 and 24H2, targeting a critical installation failure that affected users following the May 2026 Patch Tuesday release. The update brings OS builds to 26200.8524 and 26100.8524,...
Cyber Security
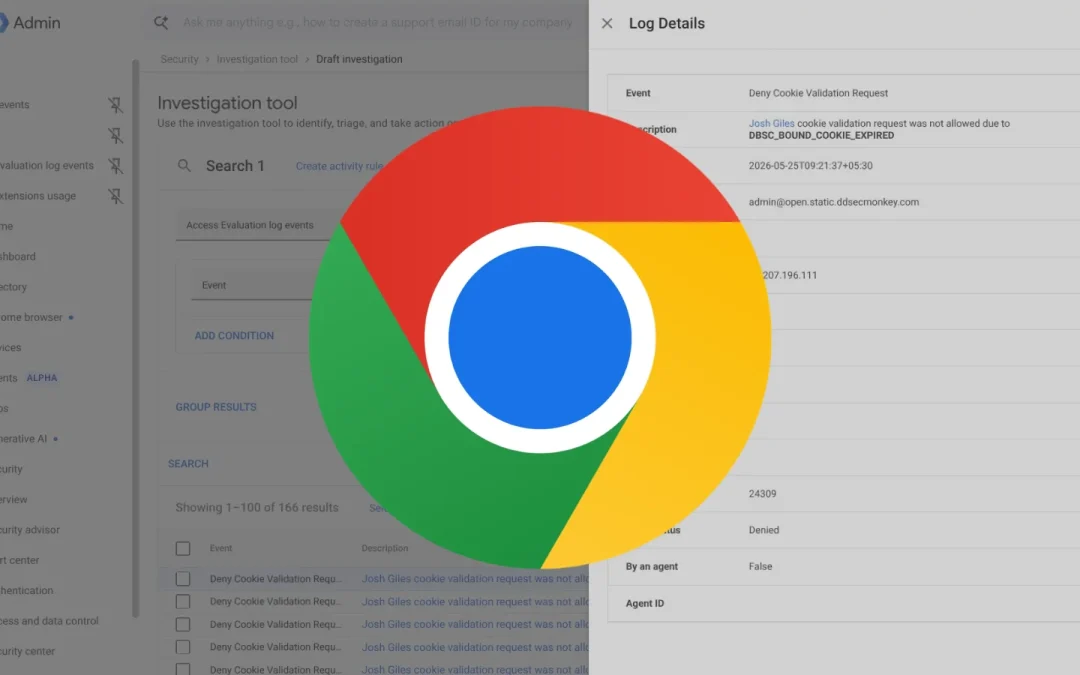
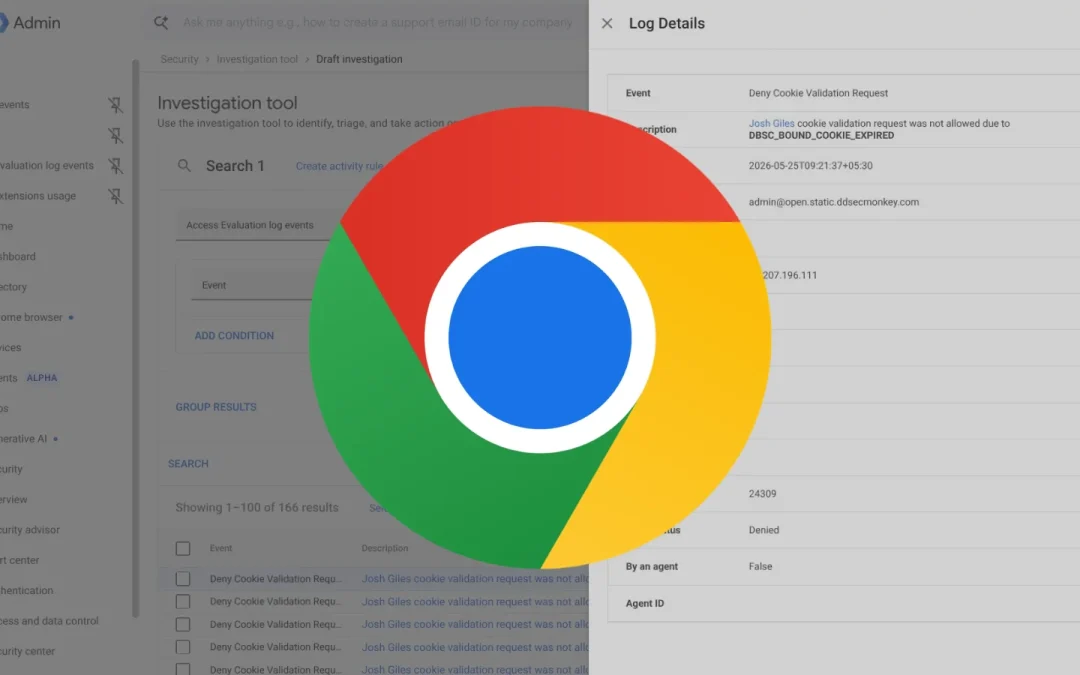
Google has officially moved Device Bound Session Credentials (DBSC) to general availability in the Chrome browser on Windows, delivering a powerful defense against one of the most persistent threats in modern cybersecurity session cookie theft. Previously available in...