Cyber Security
“`html In our rapidly evolving, interconnected environment, the threats posed by cyberattacks are becoming increasingly common and intricate. Consequently, it is crucial to remain informed and conscious of the dangers. Each week, our newsletter provides a...
Cyber Security
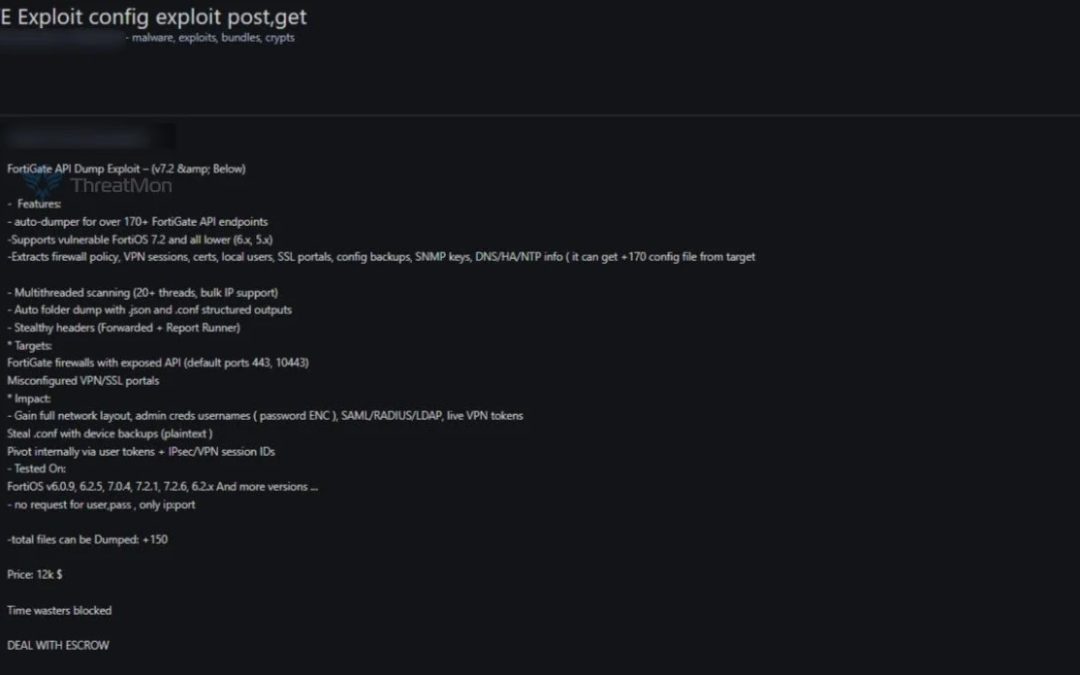
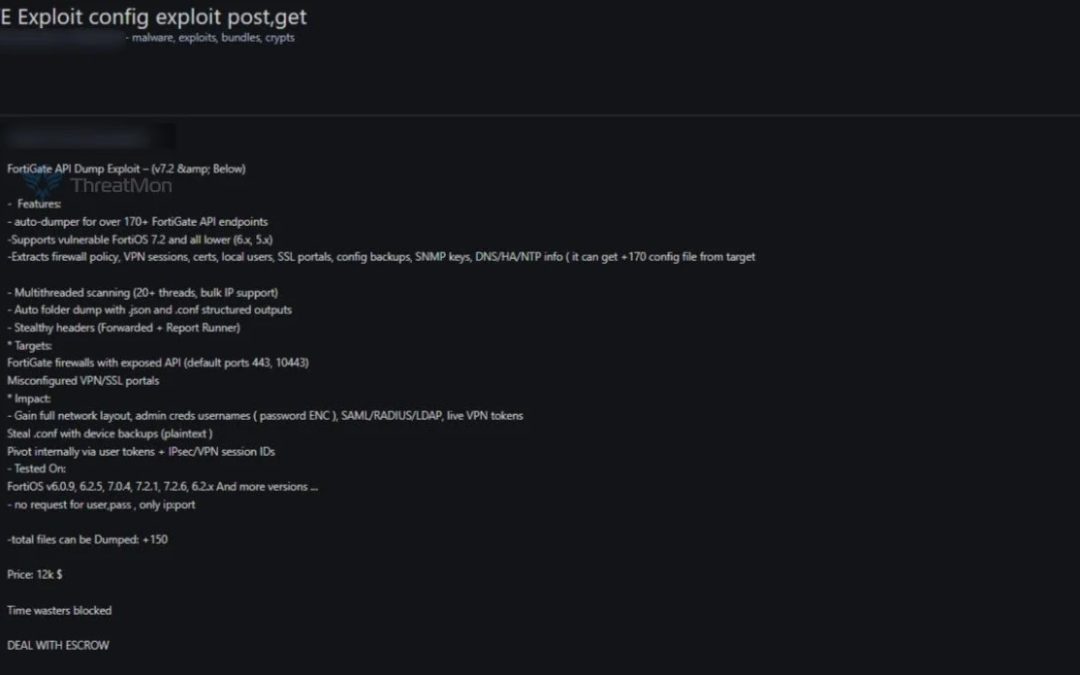
“`html A threat actor has allegedly placed a sophisticated FortiGate API exploit tool for sale on a dark web marketplace, sparking considerable alarm within the cybersecurity sector. The tool, which is being offered at a price point of $12,000 and includes...
Cyber Security
Halo Security’s Attack Surface Management Platform Recognized for Outstanding Innovation and Effective Implementation Through The Channel Halo Security has announced today that its attack surface management solution has been awarded the 2025 MSP Today Product of the...
Cyber Security
The Washington Post is undertaking an extensive inquiry into a complex cyber assault that breached the email accounts of several journalists, with cybersecurity professionals and federal agencies scrutinizing evidence that points to the involvement of a foreign...
Cyber Security
Cross-strait tensions have surged into a novel sphere as China and Taiwan partake in extraordinary reciprocal allegations of cyber warfare aimed at vital infrastructure systems. The diplomatic contention has amplified following Taiwan President Lai Ching-te’s...
Cyber Security
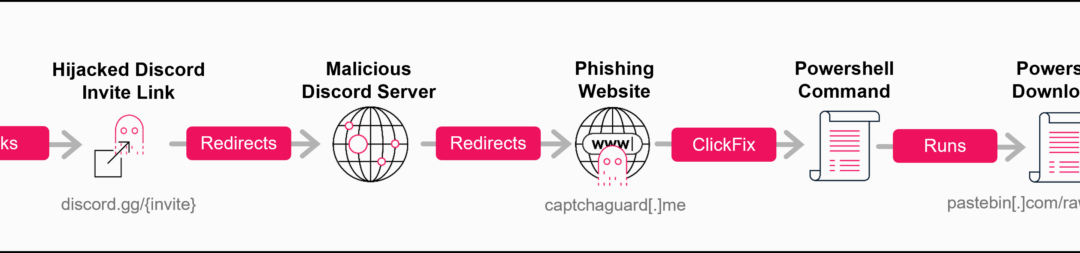
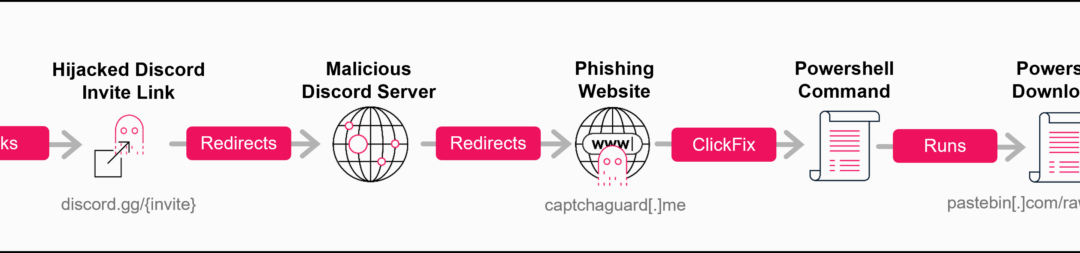
Cybercriminals have uncovered a complex new attack pathway that takes advantage of a pivotal vulnerability in Discord’s invitation framework, permitting them to commandeer obsolete invite links and reroute unwitting users to hazardous servers hosting sophisticated...
Cyber Security
“`html Secure code review is an essential security practice that thoroughly scrutinizes software source code to uncover and rectify security vulnerabilities prior to their deployment in production environments. This detailed assessment acts as a proactive...
Cyber Security
“`html Ransomware perpetrators have increasingly resorted to a refined new malware instrument known as Skitnet, also referred to as “Bossnet,” to improve their post-exploitation capabilities and bypass conventional security protocols. First surfacing on...
Cyber Security
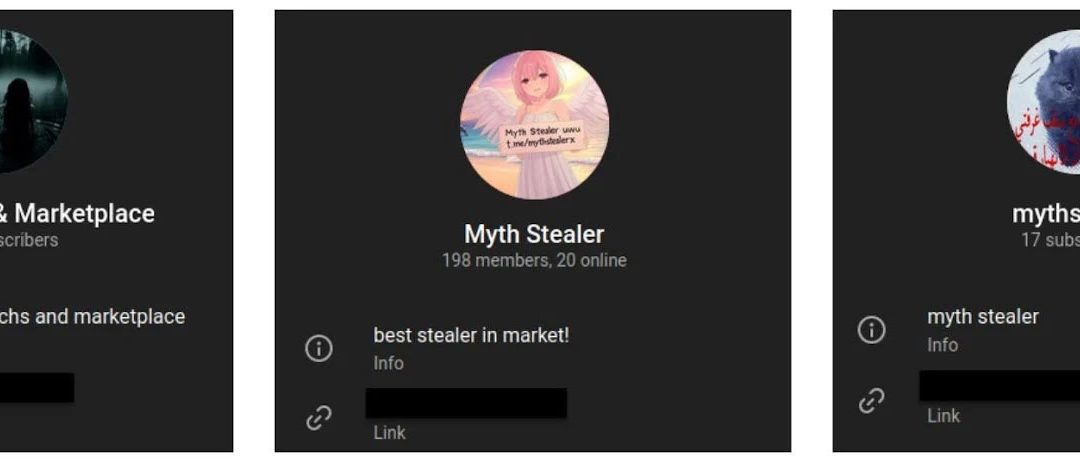
A sophisticated new data-exfiltrating malware crafted in the Rust programming language has surfaced, showcasing advanced abilities to retrieve sensitive information from both Chromium-based and Gecko-based web browsers. The malware, referred to as Myth Stealer,...
Cyber Security
Kali GPT, a tailored AI model based on the GPT-4 framework, has been specifically designed to integrate fluidly with Kali Linux, providing unparalleled assistance for offensive security experts and learners alike. Kali GPT signifies a major advancement in the...