Cyber Security
“`html The recent upgrade to the Metasploit Framework this week presents a noteworthy improvement for penetration testers and red team practitioners, unveiling seven new exploit modules aimed at widely utilized enterprise applications. The centerpiece of this...

Cyber Security
“`html Microsoft has formally launched the optional non-security preview update KB5074105 for Windows 11, versions 25H2 and 24H2. This rollout, part of the January 2026 “C-week” timeline, emphasizes feature improvements, performance enhancements, and stability...
Cyber Security
“`html By 2026, personal information is not merely a privacy issue; it has evolved into a security threat. With the emergence of AI-based data gathering and artificial identity fraud, your digital traces are being collected like never before. Data erasure...

Cyber Security
“`html A significant sandbox escape weakness has been discovered in vm2. This extensively utilized Node.js library offers sandbox isolation for running untrusted code. The issue, recorded as CVE-2026-22709 (GHSA-99p7-6v5w-7xg8), impacts all releases up to and...

Cyber Security
“`html Microsoft issued urgent out-of-band security patches on January 26, 2026, to resolve CVE-2026-21509, a zero-day vulnerability that allows circumvention of security features in Microsoft Office, actively targeted by attackers. The defect, classified as...

Cyber Security
“`html Microsoft has initiated an urgent probe into substantial stability complications affecting the January 2026 security update for Windows 11, after reports indicate that the patch is resulting in serious boot failures on physical devices. The update,...
Cyber Security
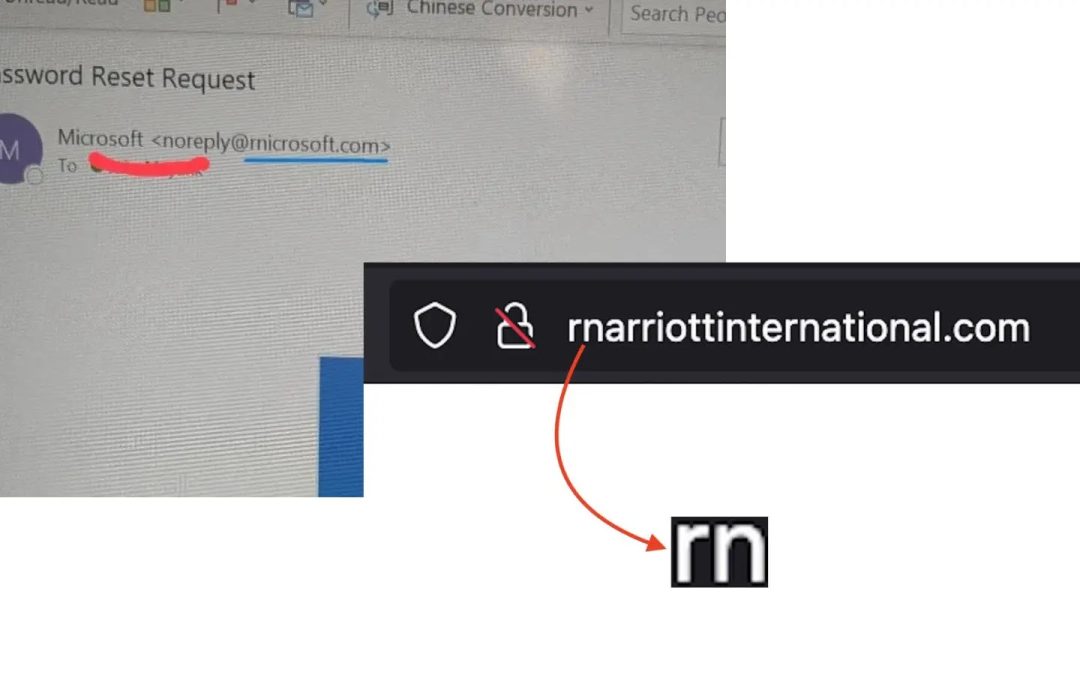
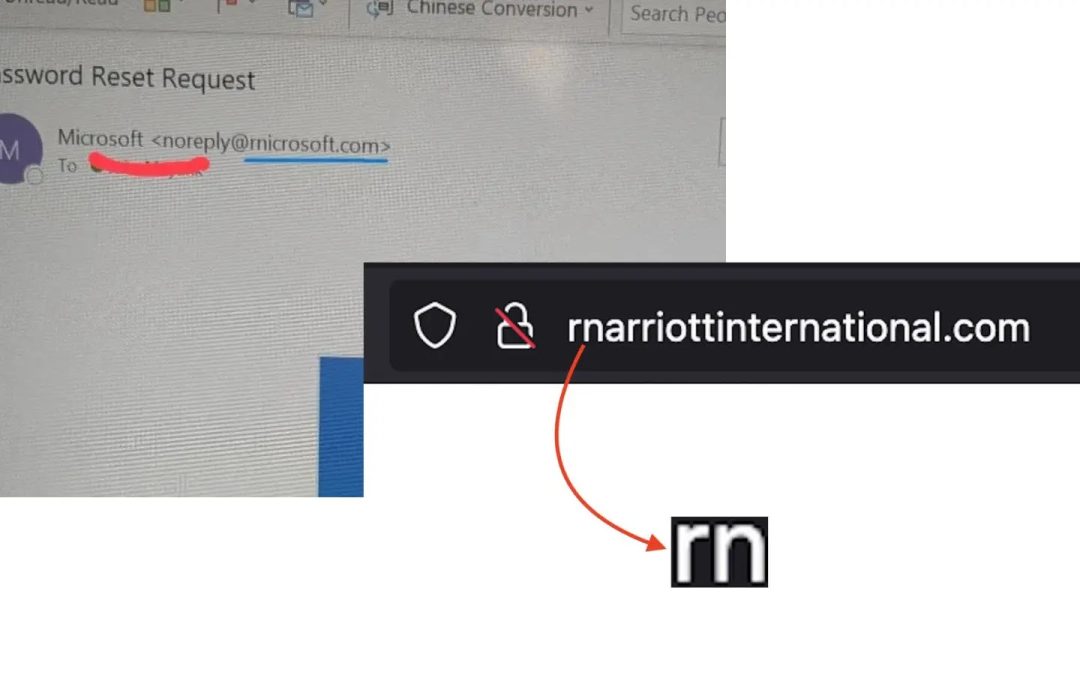
“`html A complex “homoglyph” phishing scheme aimed at patrons of Marriott International and Microsoft. Cybercriminals are registering domains that substitute the letter “m” with the pairing “rn” (r + n), generating counterfeit websites that appear remarkably...

Cyber Security
“`html Microsoft provided U.S. federal authorities the digital keys required to unlock three encrypted laptops associated with a significant COVID unemployment fraud in Guam. This situation illustrates how encryption keys stored in the cloud can assist law...
Cyber Security
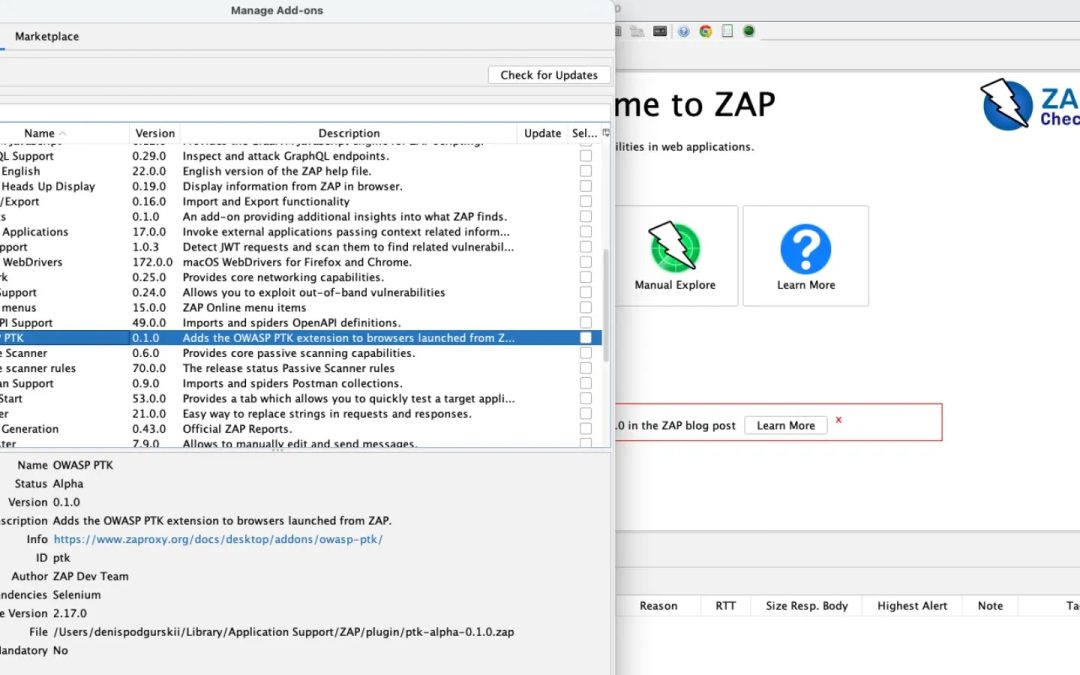
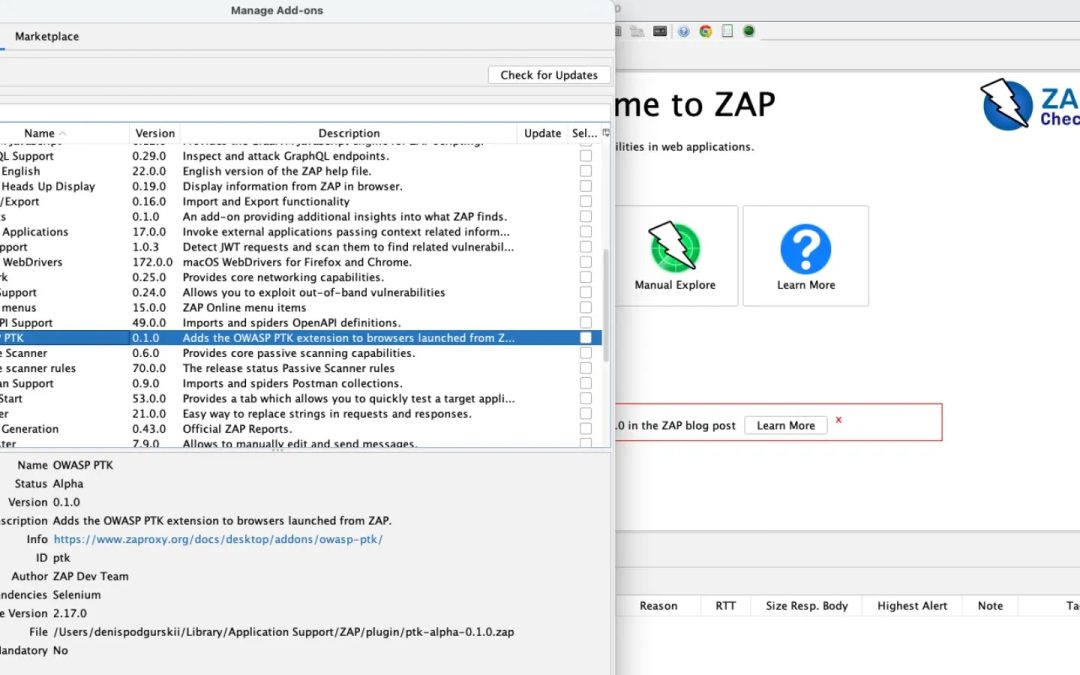
“`html The Zed Attack Proxy (ZAP) group has unveiled the OWASP PTK extension, version 0.2.0 alpha, which incorporates the OWASP Penetration Testing Kit (PTK) browser add-on directly into browsers initiated by ZAP. This enhances application security evaluation by...

Cyber Security
“`html Cisco has revealed a significant zero-day remote code execution (RCE) vulnerability, CVE-2026-20045, currently being exploited in real scenarios. This flaw impacts essential Unified Communications products, permitting unauthorized adversaries to execute...