“`html
When every moment is crucial, having immediate access to up-to-date threat intelligence is essential. This is a common feature among all high-achieving SOC teams. Discover where to obtain pertinent threat data at no cost and how to triage incidents swiftly with it.
Acquiring & Utilizing Free Threat Intelligence
Augmenting your indicators with threat intelligence is a task that must not be neglected. It provides SOCs with the information and resources necessary for achieving critical objectives of security teams, which include:
- Speeding up alert triage
- Increasing detection rates
- Minimizing alert fatigue
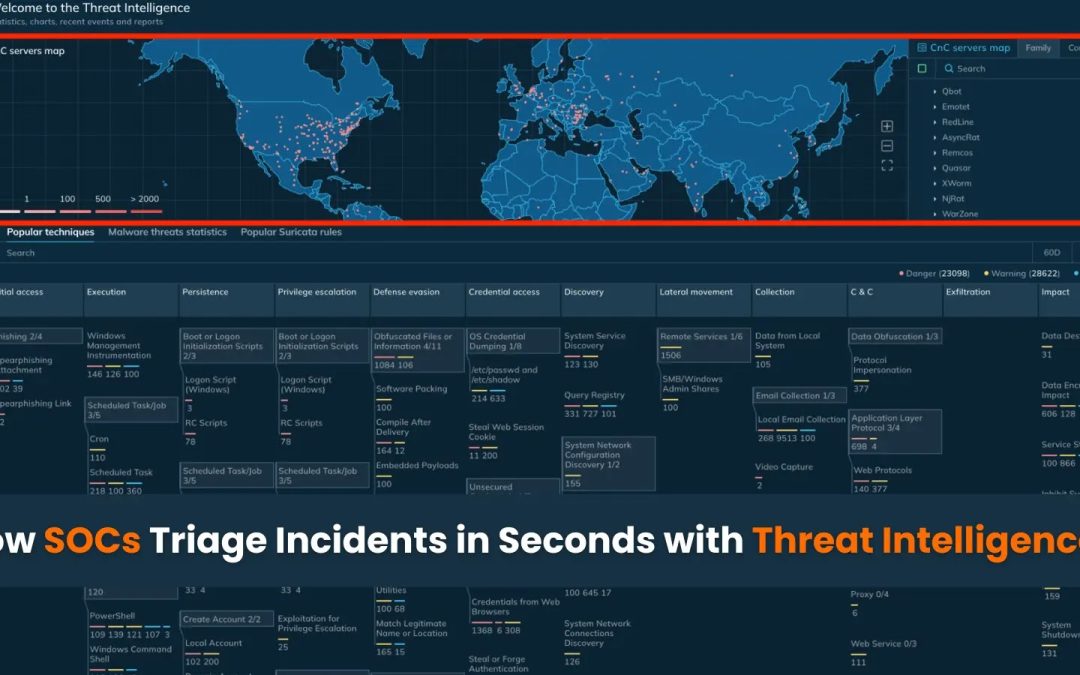
The initial action to take is locating a trustworthy source for data regarding attacks that can be accessed conveniently during triage. For this purpose, you can explore Threat Intelligence Lookup, a searchable repository of threat intelligence.
By gathering information from public malware examinations conducted by over 15,000 SOC teams and 500,000 individual researchers, it provides valuable indicators along with their context to you.
This implies that with a single straightforward query, you can access millions of malware analyses to pinpoint and enhance your indicators, as well as discover new ones for updates to proactive defense mechanisms. For example, during alert triage, you can authenticate a questionable domain using a TI Lookup query like this:
domainName:”technologyenterdo.shop”
Nearly instantly, you’ll receive the response: the indicator is malicious. More details can be found within the ANY.RUN Sandbox. This is the origin of TI Lookup’s data, ensuring that each indicator you find is associated with an appropriate analysis session.
To proactively investigate ongoing threats in your area, use a composite search like this to gather IOCs and update detection protocols ahead of time:
threatName:”tycoon” AND submissionCountry:”de”
This includes the threat’s name (Tycoon) and the abbreviated name of the nation where it was detected (de—Germany). Shortly after entering it, TI Lookup will provide an overview of relevant threats and up to 20 recent analysis sessions conducted in ANY.RUN’s Interactive Sandbox. Utilize this information for proactive identification of potential threats and renewal of detection systems.
Additional applications of Threat Intelligence Lookup consist of verifying not only domains but also IPs and file hashes, as well as monitoring threats through TTPs using an interactive MITRE ATT&CK matrix. Through these methods, TI Lookup results in significant enhancements to SOC performance metrics:
- In-depth and Swift Threat Investigations: Reveal extensive data by correlating artifacts to actual attack patterns and reduce MTTR by comprehending threat behaviors and TTPs.
- Enhanced Proactive Defense: Monitor relevant threats and remain ahead of them by crafting smarter detection rules in SIEM, IDS/IPS, and EDR.
- Improved SOC Expertise: Bridge the knowledge gap in your team—analysts can investigate malware and adversary TTPs in the interactive sandbox and MITRE ATT&CK matrix.
Premium Access to Threat Intelligence for Enterprises
The above-mentioned use cases are accessible in the free version of TI Lookup. This can suffice to simplify and expedite your threat investigations. However, if you seek an enterprise-level solution with unrestricted functionality, consider exploring TI Lookup Premium.
It grants access to additional query operators and over 40 parameters, all available analysis sessions, private searches, and YARA search capabilities. These features empower you to formulate more sophisticated requests and observe all existing threat data. The paid tier of TI Lookup can also be integrated using API and SDK for an automated and seamless workflow.
- Automated, Real-Time Detection: Correlate alerts against a broad range of IOCs, IOBs, and IOAs, while assimilating TI Lookup with SIEM, TIP, or SOAR platforms for ongoing monitoring.
- Precision Hunting & Investigation: Create and search custom YARA rules in ANY.RUN’s database, and enhance investigations with over 40 parameters and advanced operators.
- Proactive Threat Awareness: Automate alerts for specific IOCs or behaviors, and utilize expert TI Reports to remain ahead of evolving malware patterns across various sectors.
“`