Cyber Security
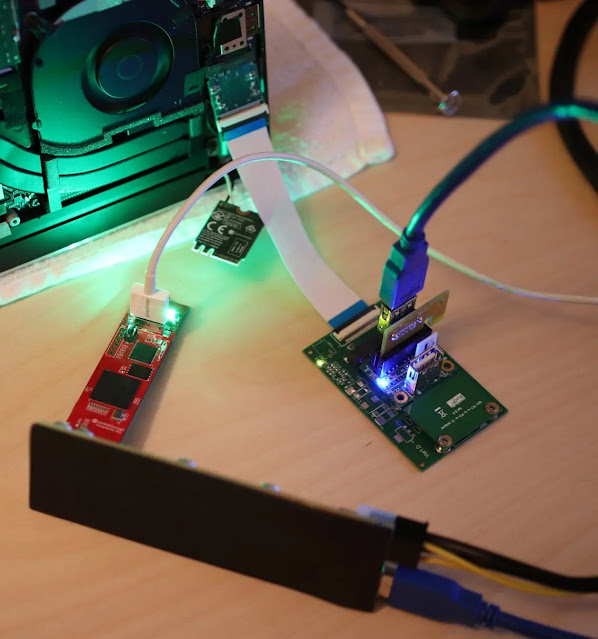
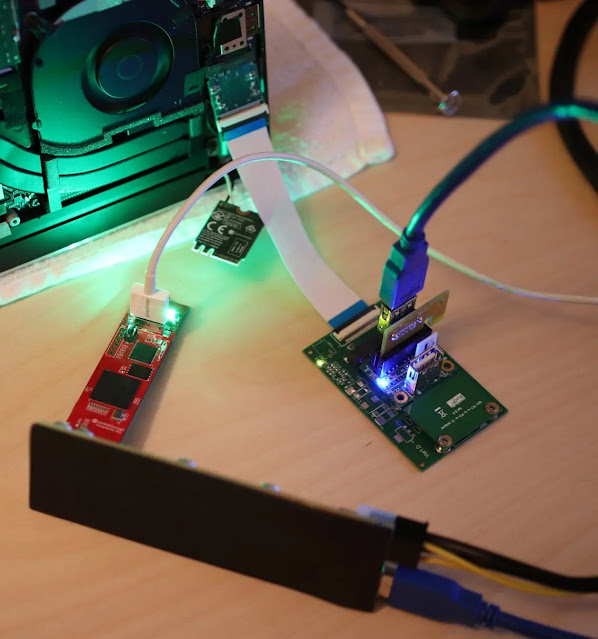
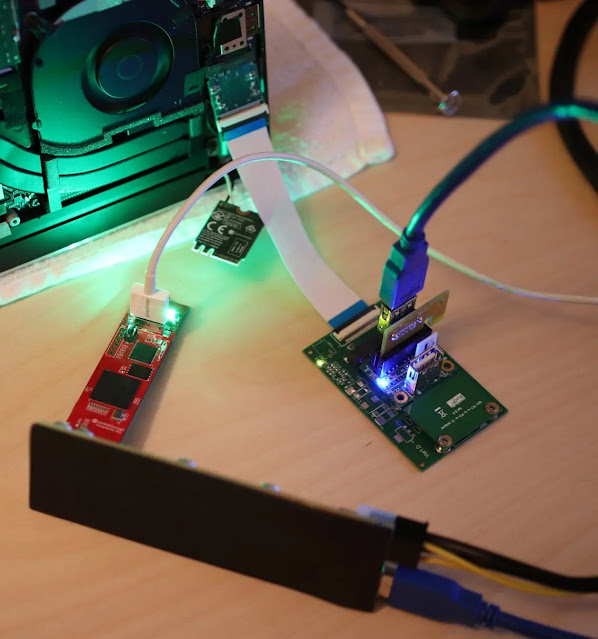
A novel form of breach, named “DaMAgeCard,” capitalizes on the SD Express standard to gain direct entry to a device’s memory through its SD card reader. This technique sidesteps conventional security measures, enabling intruders to retrieve confidential information or...
Cyber Security
Thinking of TikTok as the place to discover new recipes and chuckle at amusing clips, one cannot overlook the cybersecurity worries associated with the platform. Nevertheless, TikTok is making efforts in recent times to uphold cybersecurity standards through its...
Cyber Security
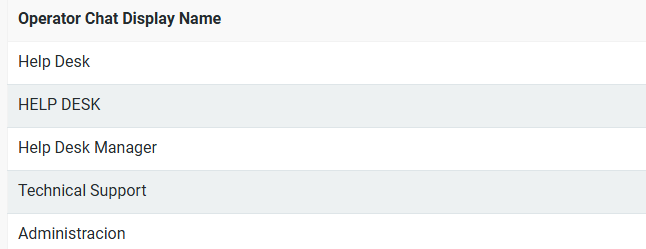
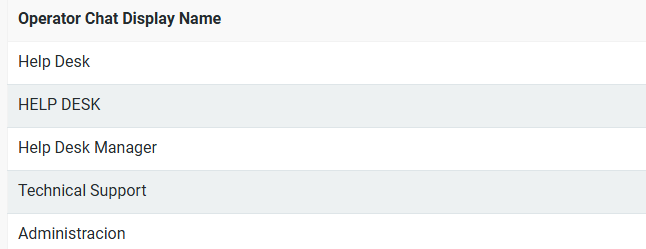
The ransomware operators of Black Basta have enhanced their strategies by utilizing Microsoft Teams to distribute Zbot, DarkGate, and Custom Malware. In an ongoing social engineering operation, a threat actor overwhelms a user’s mailbox with spam before reaching out...

Cyber Security
In 2024, there was a notable rise in the skills, assertiveness, and unpredictability of ransomware assailants. Almost all the major statistics have increased — more ransomware factions, larger targets, and higher payouts. Criminal ransomware syndicates also target...
Cyber Security
One Identity – a Hot Company: Privileged Access Management (PAM) – secured the 12th Cyber Defense Magazine’s Annual InfoSec Awards at CyberDefenseCon 2024. Victorious in the Hot Company: Privileged Access Management (PAM) category, One Identity celebrates...