Cyber Security
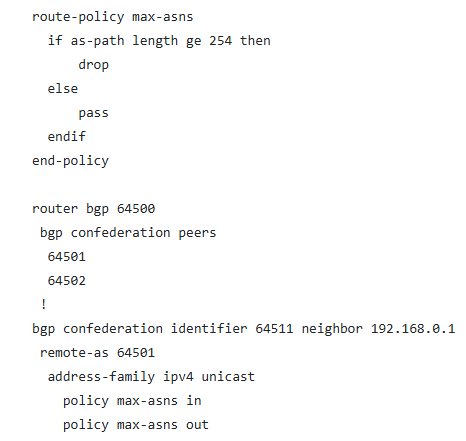
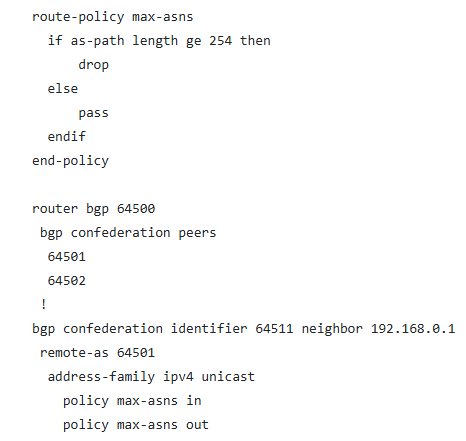
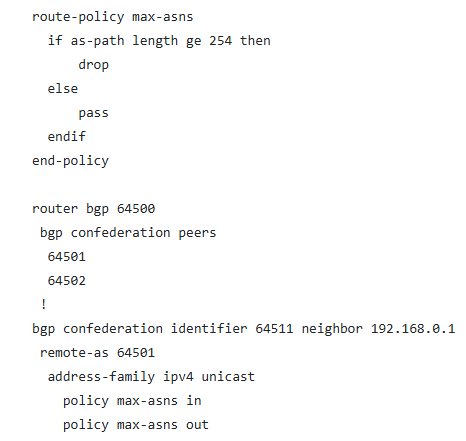
Cisco has released security notifications regarding various vulnerabilities impacting its IOS XR Software, focusing primarily on a notable memory corruption issue within the Border Gateway Protocol (BGP) confederation implementation. The identified vulnerability,...
Cyber Security
The CISA heightened its cybersecurity warning by including six critical Microsoft Windows vulnerabilities in its Known Exploited Vulnerabilities (KEV) Catalog, with four specifically impacting the New Technology File System (NTFS). These weaknesses identified as...

Cyber Security
Microsoft’s Remote Desktop Protocol (RDP) has unveiled an obscure yet pivotal security attribute informally termed as “incognito mode” utilizing its /public command-line parameter. This feature, officially labeled as public mode, bars the client from...
Cyber Security
Elastic has published an urgent security alert regarding a crucial weakness in Kibana, dubbed as CVE-2025-25012, which permits authenticated intruders to carry out random commands on impacted systems. The imperfection, scoring 9.9 on the CVSS v3.1 scale, arises from a...
Cyber Security
Essential tools for dynamic analysis of malware are crucial in identifying and comprehending present-day online dangers. These utilities operate suspicious applications in controlled environments to oversee their actions, which entail alterations in files, network...
Cyber Security
An advanced threat cluster identified as UAC-0212 has intensified efforts to breach vital infrastructure systems in Ukraine, as per a recent alert from CERT-UA (Government Computer Emergency Response Team of Ukraine). Since July 2024, these assaults have been...