“`html
An advanced iteration of Kerberoasting referred to as the “Ghost SPN” assault enables attackers to gather Active Directory credentials while eliminating all evidence of their operations, making conventional detection frameworks largely oblivious to the breach.
The assault disclosed by Trellix cybersecurity analysts employs delegated administrative rights, creating brief exposure intervals.
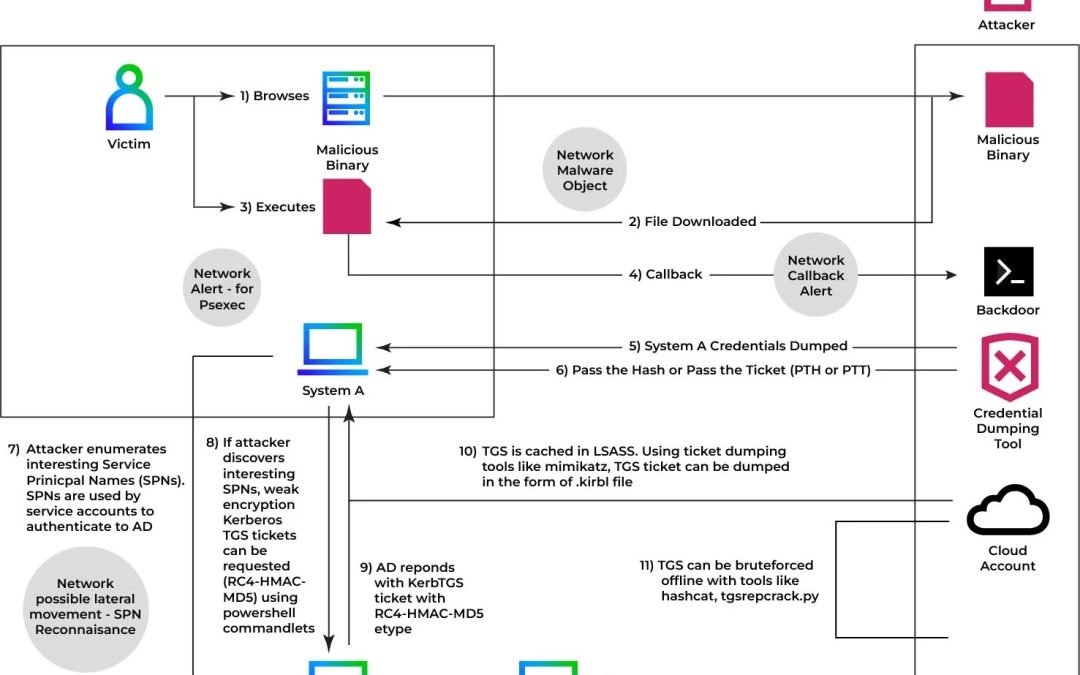
Kerberoasting is a thoroughly documented post-exploitation method that targets Active Directory (AD) accounts associated with Service Principal Names (SPNs).
When a Ticket Granting Service (TGS) ticket is sought for an SPN, the Kerberos Key Distribution Center (KDC) encrypts it using the target account’s NTLM hash, which perpetrators can harvest and dismantle offline to retrieve unencrypted credentials.
The Ghost SPN variant advances this further. Instead of listing existing service accounts, antagonists exploit delegated directory privileges, such as GenericAll object-level write access, to temporarily assign a phony SPN to a regular user account.
This transforms a typical user into a fleeting Kerberoasting target without interacting with any known service account, generating zero enumeration-based alerts in the process.
The Three-Phase Attack Lifecycle
As outlined by Trelix researchers, the attack proceeds through three intentional stages:
- SPN Allocation (Out-of-Band): The assailant utilizes write access to manually allocate a random SPN (e.g.,
http/webapp) to a target account via PowerShell commandlets. The KDC, recognizing a legitimate service principal, issues a TGS ticket encrypted with RC4-HMAC-MD5 — typical Kerberos operation with no visible anomalies at the protocol level. - Extraction and Offline Decryption: The TGS ticket is extracted using tools like Mimikatz and saved as a
.kirbifile. Decryption transpires entirely outside the environment employing tools such as Hashcat ortgsrepcrack.py, producing no authentication failures or suspicious login attempts within the target infrastructure. - Sanitation and Anti-Forensics: The SPN attribute is promptly removed, reverting the account to its previous condition. In the absence of persistent indicators, defenders relying on static directory snapshots or low-fidelity audit logs cannot retroactively associate the TGS request with nefarious activities.

This method directly undermines detection frameworks built upon two incorrect premises: that Kerberoasting targets are invariably pre-registered service accounts, and that malicious actions generate high-volume ticket request discrepancies.
The targeted account may have never maintained a service role. The SPN could exist for mere seconds. When assessed in isolation, the activity is indistinguishable from a legitimate administrative task, exhibiting a significant visibility gap in SOC frameworks that depend on fragmented log analysis.
Mitigations
Organizations should undertake the following immediate measures:
- Conduct thorough ACL audits — identify and rescind
GenericAllorWriteSPNpermissions awarded to non-administrative accounts - Activate detailed AD change logging — correlate
msDS-ServicePrincipalNameattribute changes with subsequent Kerberos ticket requests - Implement AES-only Kerberos encryption — eliminate RC4-HMAC-MD5, which is considerably more susceptible to offline cracking
- Reset passwords for compromised accounts — prioritize accounts with a history of write-access exposure to privileged objects
- Deploy behavioral NDR tools — static signature matching and SIEM-only strategies cannot detect fleeting identity manipulation without cross-domain telemetry
As adversaries progressively shift from exploiting software vulnerabilities to exploiting legitimate directory permissions, a characteristic of Living-off-the-Land (LotL) tactics, defenders must refocus from monitoring access attempts to continuous observation of identity attribute changes, particularly those designed to vanish.
“`