“`html
An information security analyst using the pseudonym Chaotic Eclipse (@ChaoticEclipse0) has made public a functional zero-day local privilege escalation (LPE) exploit for Windows, referred to as BlueHammer, along with comprehensive proof-of-concept (PoC) source code hosted on GitHub.
This revelation was verified by vulnerability analyst Will Dormann, who stated that the exploit operates effectively and that Microsoft’s own security response protocol may have inadvertently led to this uncoordinated unveiling.
BlueHammer is a Windows zero-day LPE exploit permitting a low-privileged local user to elevate their access to NT AUTHORITYSYSTEM, the utmost privilege level on a Windows device.
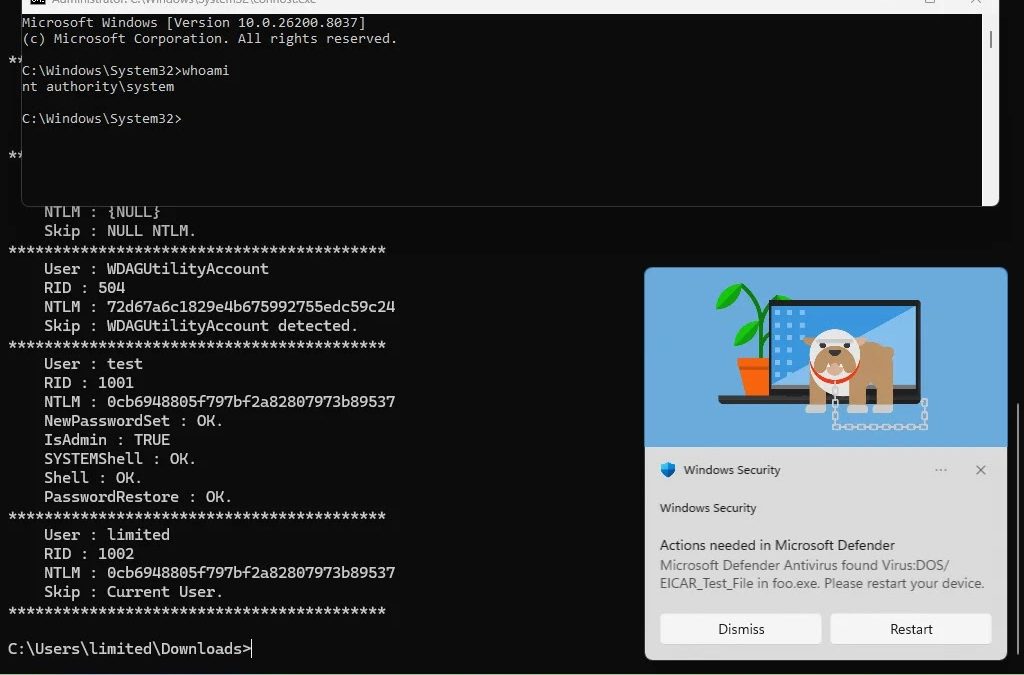
An accompanying screenshot provided alongside the announcement vividly illustrates the effect: a command prompt initiated from C:UserslimitedDownloads> — clearly indicating a restricted user account — achieves a complete SYSTEM shell almost instantaneously, with whoami confirming nt authoritysystem.

The output from the exploit also indicates credential-collection capabilities, revealing NTLM password hashes for local accounts, including an administrator user marked with IsAdmin: TRUE, and affirmations of SYSTEMShell: OK, Shell: OK, and PasswordRestore: OK.
The affected system is operating on Windows 11 (Build 10.0.26200.8037), suggesting that the vulnerability impacts contemporary, fully updated Windows installations.
The analyst expressed dissatisfaction with Microsoft’s Security Response Center (MSRC) as the main reason for the uncoordinated public revelation.
According to Chaotic Eclipse, the caliber of MSRC has markedly declined over recent years, blaming this regression on Microsoft terminating experienced security staff and substituting them with individuals adhering to strict procedural flowcharts rather than applying knowledgeable judgment.
A particularly critical detail in the revelation: MSRC allegedly mandated the researcher to submit a video demonstration of the exploit as a component of the vulnerability reporting procedure, a stipulation that many within the security community have deemed unusual and burdensome.
The researcher proposes that this requirement may have constituted a deliberate obstacle that eventually resulted in the case being closed or delayed without resolution.
This category of disclosure, sometimes referred to as a full drop or uncoordinated disclosure, is becoming increasingly prevalent when researchers believe their submissions are being disregarded or mishandled by vendors. It exerts immediate pressure on the vendor to respond, but also exposes users to risk prior to a resolution being available.
Chaotic Eclipse noted that the exploit does not operate with 100% reliability, but conceded it performs “adequately enough” to be practically useful. In the possession of a proficient threat actor, even a partially effective LPE exploit can be enhanced and weaponized.
Ransomware groups and APT threat actors often assimilate publicly launched PoC code into their arsenals within days of its release.
Countermeasures
Until Microsoft releases an official patch or mitigation advisory, security teams should adopt the following precautionary measures:
- Monitor endpoint detection and response (EDR) mechanisms for abnormal privilege escalation activities
- Limit local user rights to the bare minimum necessary for operations
- Implement enhanced logging on Windows systems to identify irregular SYSTEM-level process initiation
- Stay alert for a Microsoft Security Update or advisory addressing the BlueHammer vulnerability
As of the time of publication, Microsoft has not yet made a public statement or assigned a CVE for this vulnerability.
“`