“`html
A fresh wave of cyber offenses is impacting trucking logistics and freight brokers, with objectives extending beyond mere data theft. Perpetrators are infiltrating logistic firms digitally to appropriate tangible cargo shipments valued at millions in the physical domain.
Cargo larceny is not an unfamiliar crime, yet the manner in which it is executed has evolved significantly. The National Insurance Crime Bureau (NICB) indicates that cargo theft losses amount to billions of dollars every year, and these figures have consistently increased.
In 2025, losses attributed to cargo theft in North America escalated to $6.6 billion, primarily fueled by digital assaults, as per fleet management statistics. Criminals historically utilized force to pilfer freight.
Currently, they employ laptops, phishing messages, and remote access applications to reroute shipments without physically leaving their premises.
The pilfered goods, encompassing energy drinks, food items, and electronic devices, are rapidly sold online or dispatched overseas before companies become aware of the incident.
This threat campaign signifies a considerable transformation in the modus operandi of organized crime factions in the digital epoch.
As supply chains transitioned online, malefactors adapted accordingly. The digitization of both domestic and international supply chains has generated novel vulnerabilities, equipping organized theft groups with the necessary tools to exploit weaknesses using advanced cyber techniques.
Threat actors now breach trucking companies and freight brokers, subsequently utilizing that access to deceitfully bid on cargo shipments, coordinate transport via legitimate routes, and ultimately redirect the goods to their own channels.
Proofpoint analysts and researchers have identified this threat cluster and expressed high confidence that the actors collaborate with organized crime syndicates to execute these intricate attacks.
The initiative has been operational since at least June 2025, although indications suggest actions commenced as early as January 2025.
Since August 2025, Proofpoint has tracked nearly two dozen initiatives, with volumes varying from fewer than 10 to over 1,000 messages per initiative.
Researchers have also observed that these threat actors do not specifically target particular companies, but rather go after a diverse range of entities from small, family-owned businesses to large transportation firms.
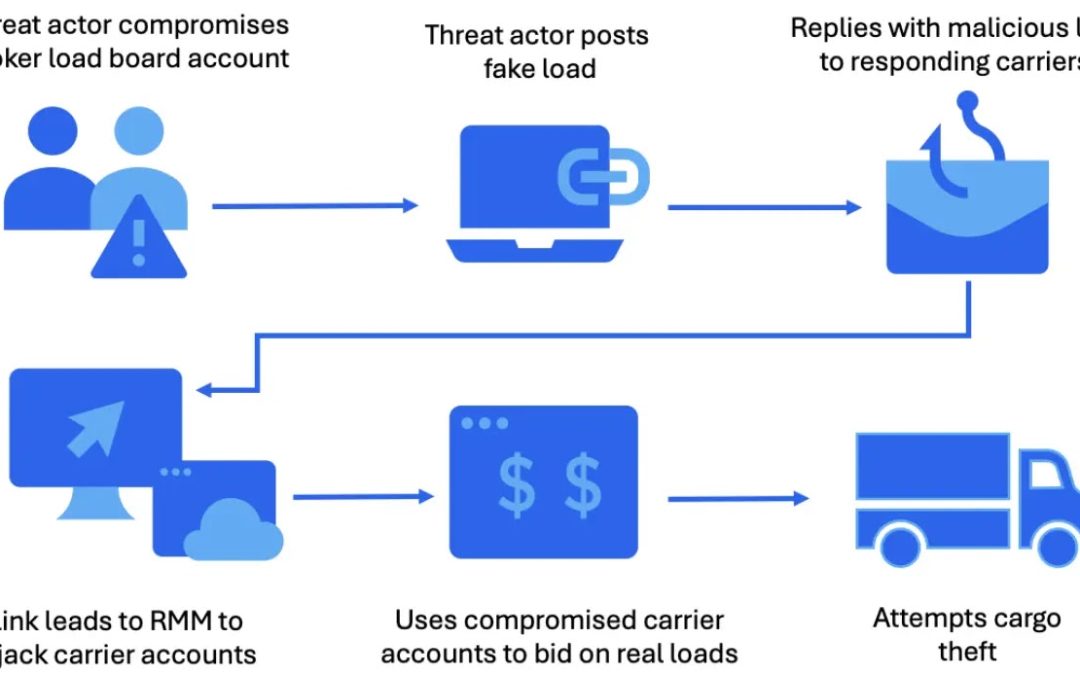
The perpetrators employ three primary tactics to gain access. Firstly, they post deceitful freight listings on hacked load board accounts to entice carriers into responding.
Secondly, they seize ongoing email threads by exploiting compromised accounts and incorporate harmful URLs into the current discussions.
Thirdly, they initiate direct email campaigns against larger organizations, including asset-based carriers, freight brokerage firms, and integrated supply chain services.
In all instances, emails contain malicious links leading to executable files (.exe or .msi files), which, once activated, quietly install a remote monitoring and management (RMM) application that grants complete control of the victim’s device.
How Perpetrators Transform a Remote Login into a Cargo Theft
Once a victim installs the RMM application, the assailant initiates a systematic process that eventually transitions from the digital realm to the physical one.
The threat cluster has been noted deploying tools such as ScreenConnect, SimpleHelp, PDQ Connect, Fleetdeck, N-able, and LogMeIn Resolve.
These represent legitimate IT solutions used by businesses for remote assistance, which precisely contributes to their efficacy as an attack apparatus.
Since the installers are certified and appear reliable, antivirus programs and network detection systems are considerably less likely to flag them.
After obtaining remote access, the attacker conducts a comprehensive system analysis, seeking credentials, active load bookings, and dispatcher data.
Credential harvesting instruments such as WebBrowserPassView are then deployed to extract saved passwords from the victim’s web browser.
.webp)
Researchers from Proofpoint discovered public exchanges on social media that align perfectly with the phishing and account takeover activities noted in these campaigns, further substantiating how extensively these approaches are disseminated among threat actors.
.webp)
The ultimate phase is where the cyber breach escalates into an actual crime. Intruders erase pre-existing freight reservations, obstruct dispatcher notifications, and incorporate their own device into the dispatcher’s phone line.
Subsequently, they rebook the load under the infiltrated carrier’s identity and orchestrate the genuine transportation of pilfered items, all while the authentic company remains oblivious.
Firms in the surface transportation sector ought to undertake the following actions to safeguard against this variety of assault. Limit the downloading and installation of any RMM tools that lack approval or verification from an organization’s IT administrator.
Implement network detection protocols, including the utilization of the Emerging Threats ruleset and endpoint protection, to notify any network activities directed towards RMM servers.
Avoid downloading and installing executable files (.exe or .msi) sent through email from unknown sources. Educate users to recognize such activities and report suspicious emails or links to their security teams, which can be easily incorporated into an existing user training initiative.
Entities susceptible to cargo theft might also gain from reviewing the National Motor Freight Traffic Association’s Cargo Crime Reduction Framework for supplementary advice.
“`